Table of Contents
Table of Contents
Are you ready to put on your detective hat and become a master network sleuth? We rely on our network to be the backbone of our businesses. From your Internet, to your VPN, to running VoIP and Unified Communication applications (like Zoom), networks have large responsibilities. But how can you know if your network is performing as it should be? That’s when you perform a network assessment.
Performing a network assessment may seem like a daunting task, but with the right tools and techniques, you can uncover hidden weaknesses and vulnerabilities in your network infrastructure like a seasoned detective.
In this blog post, we'll show you how to perform a network assessment like a network detective, from mapping out your network topology to identifying potential security threats and what network assessment questionnaire to follow. So grab your magnifying glass and let's get started!
A IT network assessment is an in-depth network infrastructure analysis to collect and analyze comprehensive data about your network’s health, including current network issues, any signs of network performance degradation, and places for improvement or network optimization.
The purpose of a network assessment is to identify any weaknesses or vulnerabilities in the network, as well as to evaluate its capacity, security, and overall health.


Network Assessments are an essential risk management tool and should be performed to qualify your network for a new service deployment or migration such as:
- Migration from on-premise VoIP PBX to hosted VoIP
- Migration from VoIP to Microsoft Teams or other UC platforms
- Migrating from an MPLS network to an SD-WAN network
- Migrating from an on-premise ERP to a cloud-based ERP
- Implementing a new SASE architecture
- Or any other on-premise to cloud migrations
Looking to solve your network issues and perform a network assessment to get complete visibility? Unlock valuable insights into your network's performance with Obkio's end-to-end network performance monitoring solution today. Don't let any missing pieces hold you back - start your free trial now and see the full picture of your network's performance.
- 14-day free trial of all premium features
- Deploy in just 10 minutes
- Monitor performance in all key network locations
- Measure real-time network metrics
- Identify and troubleshoot live network problems

Network performance is a key compoment to ensuring that a business' core applications and services and functioning at peak performance and employees can work at maximum efficiency. Large enterprise networks have so many moving parts, so it's important to check in to ensure everything is working as it should be.
When it's not, that's when the real detective work comes in: The Network Assessment.
Here are some of the benefits of a network assessment:
- Identify Network Vulnerabilities: A network assessment can help to identify security weaknesses or vulnerabilities in your network that can be exploited by cybercriminals. This can help you to take steps to address these vulnerabilities and prevent cyber attacks.
- Improve Network Performance: A network assessment can help to identify bottlenecks and other performance issues in your network. By identifying these issues, you can take steps to improve network performance, such as upgrading hardware or software, reconfiguring the network, or optimizing network settings.
- Optimize Network Resources: A network assessment can help to identify underutilized or overutilized network resources, such as servers, storage devices, and network bandwidth. By optimizing the use of these resources, you can improve network performance and reduce costs.
- Plan for Network Upgrades: A network assessment can help you to plan for future network upgrades and expansions. By identifying current network capacity and usage patterns, you can anticipate future needs and plan for upgrades and expansions accordingly.
- Ensure Compliance: A network assessment can help to ensure that your network infrastructure meets regulatory compliance requirements, such as HIPAA, PCI DSS, or GDPR. By identifying compliance gaps, you can take steps to address these gaps and avoid costly fines and penalties.
Overall, a network assessment can provide valuable insights into the performance, security, and compliance of your network infrastructure, allowing you to optimize network resources, improve performance, and mitigate security risks.
Network assessment is like a check-up for your network. Just like how you go to the doctor to make sure everything's running smoothly, network assessment techniques help ensure that your network is healthy, secure, and performing at its best. Let's dive into some of the network assessment tools and techniques!
Network monitoring is a crucial aspect of network assessment that involves the continuous surveillance of network traffic, system performance, and overall network health. The purpose of network monitoring is to identify potential problems and anomalies in the network's behavior, as well as to gather data for analysis and performance optimization.
- Packet sniffing: This technique involves capturing and analyzing the data packets that flow across the network. Packet sniffers can detect and analyze network traffic in real-time, providing insights into network performance, security, and user behavior.
- Network flow analysis: Network flow analysis involves collecting data on network traffic patterns, such as the volume and frequency of data transfers, and analyzing this data to identify trends and anomalies. This technique can be used to identify potential network congestion, security threats, and other issues.
- Performance monitoring: Performance monitoring tools can track key metrics such as CPU usage, memory usage, and network bandwidth utilization. These metrics can be used to identify potential bottlenecks and other performance issues that may be impacting network performance.
- Event log analysis: Event log analysis involves reviewing system and application logs to identify potential issues and security threats. This technique can be used to detect unauthorized access attempts, malware infections, and other security incidents.
Overall, network monitoring is an essential technique for assessing network performance, identifying potential issues and security threats, and optimizing network performance. By using a variety of monitoring tools and techniques, like Obkio Network Monitoring tool, network administrators can ensure that their networks are running smoothly and securely.
Network mapping is a beneficial technique for network assessment that involves creating a visual representation of the network's components and connections. The purpose of network mapping is to provide a clear overview of the network's structure, enabling administrators to identify potential vulnerabilities, performance issues, and other areas that may require optimization.
Network mapping can be done manually or using automated tools. In manual mapping, network administrators physically inspect and document the network's components and connections, including routers, switches, servers, workstations, and other devices. This process can be time-consuming and prone to errors, particularly in large or complex networks.
Once the network map is created, network administrators can use it to identify potential issues and areas that may require optimization. For example, they can identify network bottlenecks, unused or underutilized resources, outdated hardware or software, and potential security vulnerabilities.
Traffic analysis is another technique used for network assessment, which involves the study and analysis of network traffic. The purpose of traffic analysis is to understand how data flows through the network, identify potential bottlenecks or congestion, and detect any anomalies or security threats.
There are several approaches to traffic analysis, including:
- Protocol analysis: Protocol analysis involves examining network traffic to understand the various network protocols in use, such as TCP/IP, HTTP, FTP, and SMTP. By analyzing protocol headers and payloads, network administrators can identify potential issues, such as misconfigured or malfunctioning devices, and optimize network performance.
- Network packet analysis: Network packet analysis involves capturing and analyzing individual packets of data that flow across the network. By examining packet headers and payloads, network administrators can gain insights into network behavior, performance, and security. For example, they can identify unauthorized access attempts, malware infections, or other security incidents.
- Flow analysis: Flow analysis involves monitoring network traffic patterns, such as the volume and frequency of data transfers. By analyzing these patterns, network administrators can identify potential network congestion, performance issues, or other anomalies that may require optimization.
Traffic analysis can be performed manually or using automated tools, such as network packet analyzers or flow monitoring tools. These tools enable network administrators to capture and analyze network traffic in real-time, making it easier to detect and respond to potential issues or security threats.
Vulnerability Scanning is another technique used for network assessment that involves identifying potential vulnerabilities in network devices, systems, and applications. The purpose of vulnerability scanning is to proactively identify potential security threats and take appropriate measures to mitigate them before they can be exploited.
Vulnerability scanning is typically performed using automated tools that scan network devices, systems, and applications for known vulnerabilities. These tools use a database of known vulnerabilities, along with testing scripts, to scan for vulnerabilities in network devices, such as routers, switches, firewalls, and servers, as well as in software applications, such as web applications and operating systems.
Once the vulnerability scan is complete, the scanning tool generates a report that identifies potential vulnerabilities and provides recommendations for mitigating them. Network administrators can use this report to prioritize and plan remediation efforts based on the severity of the vulnerabilities and the potential impact on network security.
Performance testing is a technique used for network assessment (which invovles network testing), which tests the network's ability to perform under various conditions, such as heavy traffic or high network loads. The purpose of performance testing is to identify potential performance bottlenecks and optimize the network's performance and reliability.
Performance testing can be performed using a variety of techniques, including:
- Load testing: Load testing involves simulating heavy traffic or high network loads to test the network's ability to handle these conditions. Load testing can help identify potential bottlenecks, such as slow response times or dropped packets, and enable network administrators to optimize network performance.
- Stress testing: Stress testing involves testing the network's ability to perform under extreme conditions, such as sudden spikes in traffic or denial-of-service (DoS) attacks. Stress testing can help identify potential vulnerabilities and enable network administrators to prepare for and respond to potential security incidents.
- Bandwidth testing: Bandwidth testing involves measuring the network's available bandwidth and identifying potential bottlenecks or congestion points. This can help network administrators optimize network performance and ensure that the network is running at its maximum capacity.
Performance testing can be performed manually or using automated tools. Automated performance testing tools enable network administrators to simulate various network conditions and measure network performance metrics, such as response times, throughput, and packet loss. These tools can also generate reports that identify potential performance issues and provide recommendations for optimizing network performance.
security testing is a technique used for network assessment that involves testing the network's security posture and identifying potential vulnerabilities and security threats. The purpose of security testing is to proactively identify potential security risks and take appropriate measures to mitigate them before they can be exploited by cybercriminals.
Security testing can be performed using a variety of techniques, including:
- Penetration testing: Penetration testing involves simulating a real-world attack on the network to identify potential vulnerabilities and security threats. Penetration testers use a variety of tools and techniques to simulate attacks, such as exploiting known vulnerabilities or social engineering tactics, to gain access to the network.
- Vulnerability scanning: Vulnerability scanning involves scanning the network for known vulnerabilities and providing recommendations for mitigating them. Vulnerability scanning tools use a database of known vulnerabilities and testing scripts to identify potential vulnerabilities in network devices and software applications.
- Threat modeling: Threat modeling involves analyzing the network's architecture and identifying potential security threats and vulnerabilities. Threat modeling can help network administrators understand the network's security posture and develop strategies for mitigating potential security risks.
- Compliance testing: Compliance testing involves testing the network's compliance with industry regulations and standards, such as HIPAA or PCI-DSS. Compliance testing can help identify potential compliance issues and enable network administrators to take appropriate measures to ensure compliance with regulatory requirements.
Once the network assessment is complete, a report is generated that summarizes the findings and provides recommendations for addressing any issues or weaknesses that were identified. The report may include information on how to optimize network performance, improve security, and increase the network's capacity to handle future growth.
Trying to perform a network infrastructure assessment without a tool to help can be time consuming, and frankly can’t give you the same level of detail. So you need the help of a Network Detective - which we call a Network Performance Monitoring Tool.
The best network assessment tool is Obkio Network Monitoring. Obkio perform tests from all ends of your network to pinpoint performance issues or identify any weaknesses that may cause problems in the future.

- Network Monitoring Agents are deployed at key network locations
- Obkio sends and monitors synthetic data packets through your network every 500ms
- Obkio's Agents collect valuable data about your network health
Use Obkio’s free trial to perform a free network assessment (POC) to quickly determine if your network is causing problems, and gather information to help you troubleshoot.

You may perform a network assessment for a variety of reasons, so it’s important to consider your objectives to know what you expect from the results.
- Why do you want to perform a network assessment?
- Are you looking to identify intermittent network problems that are impacting your network?
- Are you looking to optimize network performance?
- Are you preparing your network for a new service deployment or migration?
- Are you performing an overall network health check to assess the status of your network and make proactive decisions before anything goes wrong?
To assess and compare network performance data over time, you must first measure key network metrics associated with network performance and collect a history of the data you’ve measured.
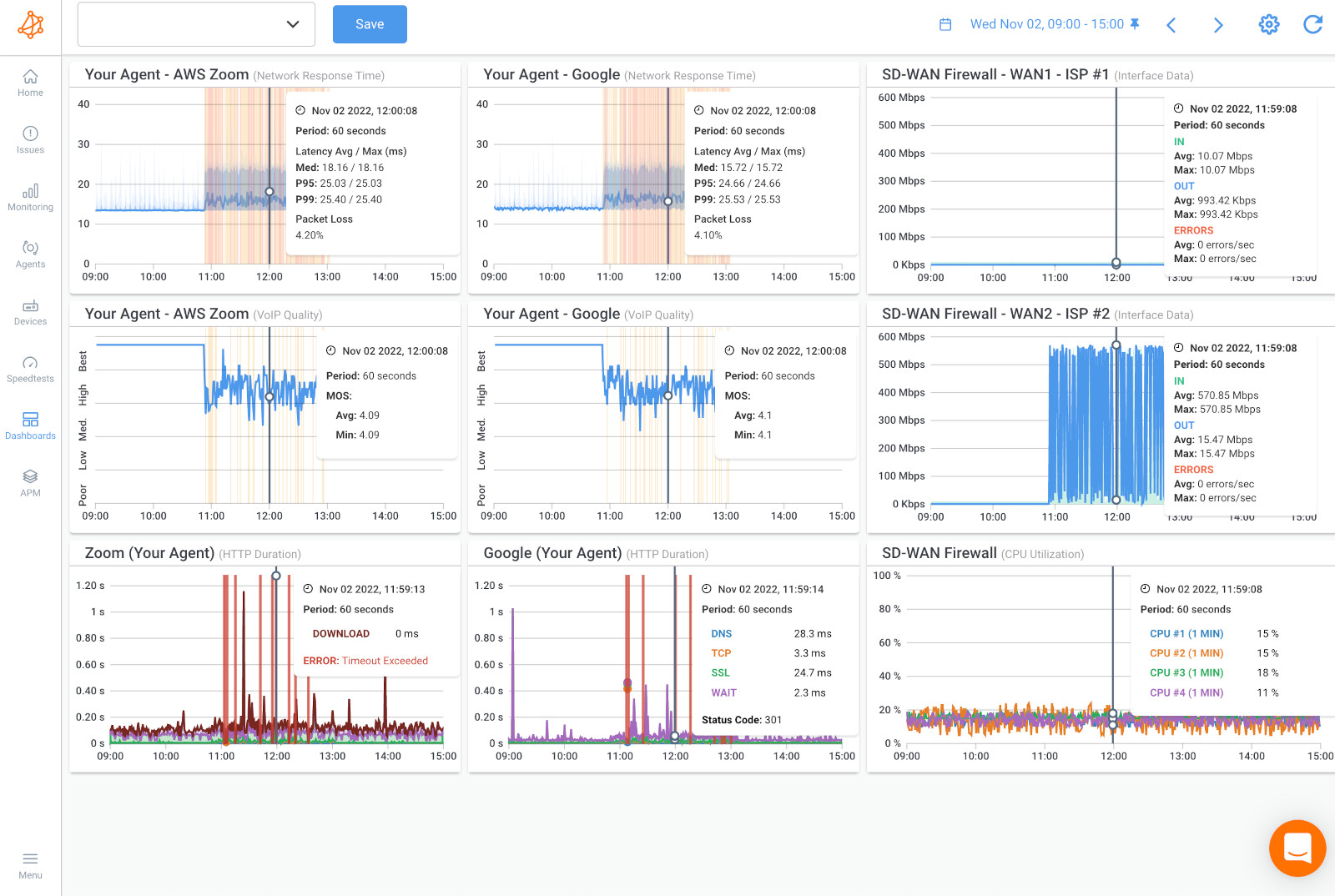
Once you’ve set up your Obkio Monitoring Agents, they will start measuring key network metrics like:
- Jitter: Measure the variation in latency over time. Jitter can disrupt real-time applications and cause inconsistencies in data delivery. Monitoring jitter helps identify areas where variations are significant and take corrective actions to minimize its impact.
- Packet Loss: Measure the percentage of packets that are lost during transmission. Packet loss can result from network congestion, hardware issues, or other factors. Excessive packet loss can cause data retransmission and impact the performance of applications.
- Latency: Measure the delay in transmitting data packets across the network. High latency can negatively impact real-time applications like video conferencing and VoIP. Monitoring latency helps identify areas where delays are occurring and take appropriate measures to optimize performance.
- Network Throughput: Measure the amount of data transferred over the network within a given time frame. Throughput indicates the efficiency of data transmission and helps identify any limitations in the network infrastructure.
- Bandwidth: Measure the available bandwidth to determine the capacity of the network and ensure it can handle the expected traffic load. This metric helps identify any bottlenecks or potential bandwidth limitations.
- VoIP Quality: Assess the quality of Voice over Internet Protocol (VoIP) calls transmitted over the network. VoIP quality metrics evaluate the clarity, reliability, and consistency of voice communication. This includes measuring factors such as mean opinion score (MOS), signal-to-noise ratio (SNR), delay, VoIP jitter, and packet loss specific to VoIP traffic. VoIP monitoring helps identify any issues that may affect the voice communication experience, such as poor audio quality, dropped calls, echo, or VoIP latency issues.
- Error Rates: Measure the error rates encountered during data transmission. This includes metrics such as bit error rate (BER) and frame error rate (FER). High error rates may indicate issues with network components or environmental factors affecting data integrity.
- Quality of Service (QoS): Assess the effectiveness of QoS mechanisms in place to prioritize critical network traffic. Measure metrics related to QoS, such as delay, jitter, and packet loss, to ensure that the network is delivering the required performance for specific applications or services.
- Network Utilization: Measure the percentage of network capacity being utilized. Monitoring network utilization helps identify peak usage periods and potential bottlenecks that may impact overall network performance.
- Network Security: Evaluate the security posture of the network by measuring metrics related to firewall rules, intrusion detection systems, access control lists, and other security measures. Assessing these metrics helps identify vulnerabilities and ensure network security best practices are in place.
Measuring these network metrics allows you to quickly understand and identify any performance issues in your network, which is one of the most important objectives of performing a network assessment.
Obkio provides metric updates every minute so you can get real-time metric measurements. You can also further drill-down to identify exactly what and where is causing network problems.
When performing a network assessment, you need to analyze every end of your network - that include network devices. The Network Device Monitoring feature inside of Obkio’s Network Monitoring Software using SNMP monitoring is then a key tool for that.
Monitor network devices such as Routers, Switches, Firewalls, SD-WAN Edge Devices, and more to identify any problems that may be affecting your network performance such as:
- CPU usage
- Bandwidth Interface Errors
- Interface Errors
- Device Availability
- CRC Errors
- Interface Duplex
This way, your IT team can quickly detect the short bursts of traffic (packet bursts), high CPU usage, bandwidth congestion or network congestion that affect network performance and pinpoint the root cause of the performance issue.
Analyzing historical performance data is key to understanding how your network is actually performing. To get an accurate network assessment, it’s important to analyze performance data over time to catch intermittent issues.
That’s why Obkio’s solution also measures and collects historical network performance data, so you can analyze, compare, and troubleshoot performance from the past.
Analyzing historical data allows you to go back in time to identify and troubleshoot intermittent network problems that may look like they disappeared.
Obkio will provide you with all the data you need to properly assess your network performance. You can even create your own dashboard with a summary of your network metric measurements, the results of speed tests, and a detailed analysis of any network issues that may have been discovered.
You can identify:
- What the problem is
- Where the problem is located
- What caused the problem
- When the problem happened
- Who is responsible for the network segment
Identifying network problems should be a key objective when performing a network assessment. Network problems, even intermittent ones, can frustrate users, affect your business operations, and cause bigger headaches in the future.
To help you really identify network problems, Obkio uses aggregation to show you the worst metric measurements in order to highlight network issues, where they’re located and what’s causing them.
For example, when testing packet loss, the packet loss displayed over an aggregated period of 1h is the worst packet loss of all the small 1-min periods in the hour.
This is key because only showing you the average amount of packet loss on your network may hide intermittent network issues.
If you measure the average packet loss every 4 hours, the average may be good, but you can have 80% during a few minutes - which signals a big problem.
Learn how to identify network issues by looking at common problems, causes, consequences and solutions.
Learn more

With all this data you’ve collected from Obkio’s app, you can then finish off your Network Assessment with your Network Performance Reports. The reports will provide you with a executive summary of your network performance health, and any network issues that were identified.
- Get Digestible Data: The network reporting allows you to collect and analyze specific network performance data in an easily digestible and shareable format.
- Share Network Data Internally: Obkio’s network performance reports can be used and shared internally to gain important, actionable insights with your team and make quick decisions after your network assessment.
- Share Network Data Externally: When you’re trying to resolve a network problem with your Service Provider, it’s important to provide them with as much information as possible, so they can quickly escalate your case past Level 1 Support. Use and generate reports to share with your Service Provider when you open a support ticket.
- Make Faster Decisions: Using a network performance report, you can quickly make informed decisions about your network’s optimization and health based on both current and historical network performance data and metrics.
- Proactively Optimize Network Performance: By examining network reports and viewing capacity usage trends, you may be able to forecast, detect, diagnose, and troubleshoot network issues before complete network outages occur.
- Monitor SLA Agreements: Network performance reporting is also critical for monitoring the compliance with SLAs or service-level agreements. Gather and view the information to prove that service or Internet SLAs are being met, or to prove to your Service Provider that they’re not complying with your service-level agreement.
Once you’ve performed your network assessment and identified network problems, you need to troubleshoot network issues and optimize network performance.
A great network monitoring tool will allow you to collect the data you need for network troubleshooting with your IT or network team, or share the data with your Service Provider for faster troubleshooting.
When troubleshooting network problems, several tools are available to help:
- Traceroutes: to identify route, latency and packet loss between two sites and detect exactly where and when network problems happened. You can also view traceroute results with Obkio Vision Visual Traceroute tool and share traceroute results with your Service Provider to help them troubleshoot.
- Network Device Monitoring: to get detailed information about the health of network devices such as firewalls, routers, switches and wifi access points. It can also help you identify if network problems are located in your LAN, on your Firewall or in your Internet Service Provider’s network.
- Speed Tests: which allow you to validate if the bandwidth you need is readily available.
- Prioritization and QoS: which increases network efficiency in the event of network congestion (WAN or LAN congestion) and prioritizes applications more critical or sensitive to performance problems such as VoIP or video.

Congrats! You've completed your network assessment - but network optmization doesn't end there. A Network Detective's work is never done!
The key to getting the most out of a network assessment is to take action on the findings and recommendations, and to regularly review and update your network to keep pace with changing business needs and security threats.
After a network assessment, there are several steps you can take to act on the findings and improve your network:
- Keep Monitoring Network Performance: While monitoring network performance is a key part of assessing the current health of your network and identifying current issues, it's also important for ensuring that your network performance is always at it's best. After your network assessment, keep Obkio as your permanent Network Monitoring Detective to proactively identify network problems and continue to find ways to optimize network performance.
- Prioritize Recommendations: Review the recommendations and findings from the network assessment and prioritize them based on their importance and potential impact on your network. Some recommendations may be critical and require immediate attention, while others may be lower priority.
- Develop an Action Plan: Develop an action plan that outlines the steps you need to take to address the recommendations from the network assessment. The action plan should include timelines, responsible parties, and specific tasks that need to be completed.
- Implement Changes: Implement the changes recommended in the network assessment action plan. This may involve upgrading hardware or software, reconfiguring the network, or changing security settings. Be sure to document any changes made to the network for future reference.
- Test the Network: After implementing changes, test the network to ensure that the changes have been effective and have not introduced any new problems or vulnerabilities.
- Schedule Follow-Up Assessments: Schedule follow-up network assessments to monitor the effectiveness of the changes made and to identify any new issues that may have arisen.
- Maintain Network Security: Regularly review and update your network security policies and procedures to ensure that your network remains secure and compliant with regulatory requirements.
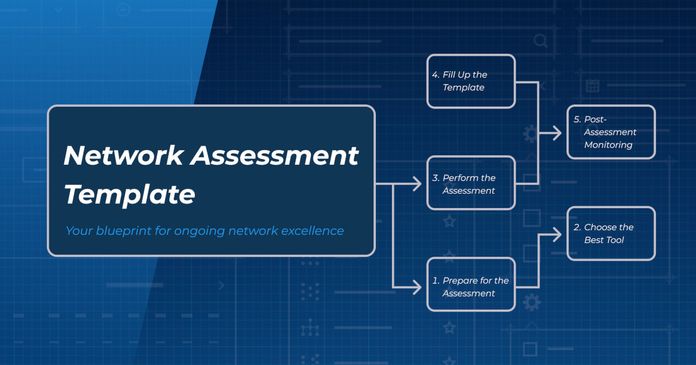
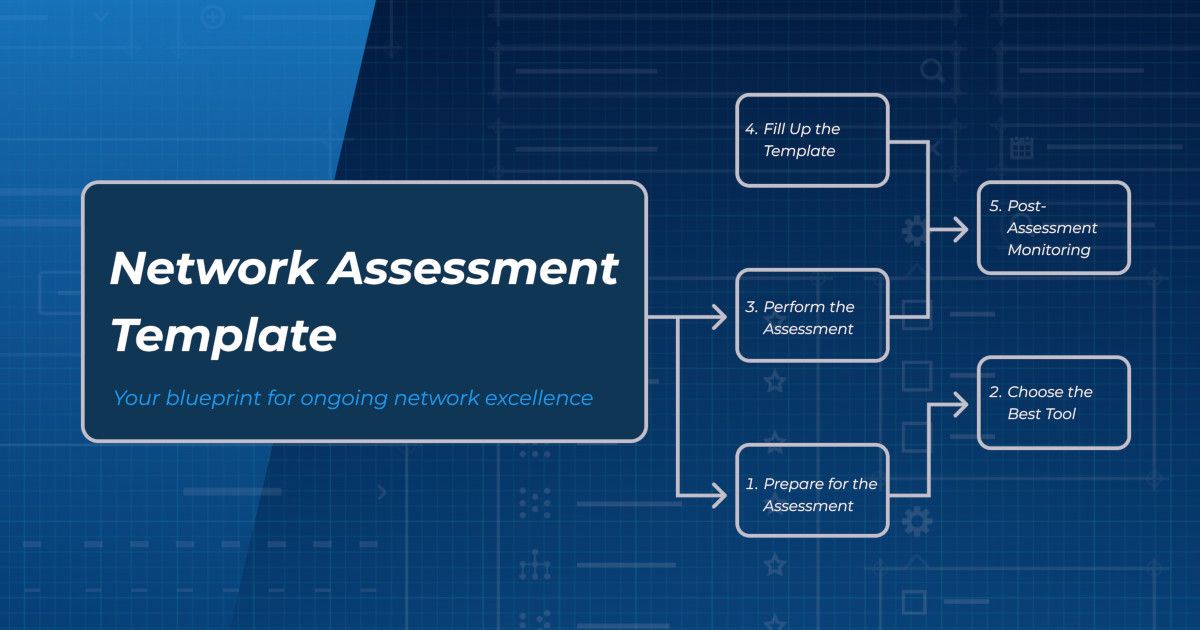
Unlock the power of network assessment with our step-by-step network assessment template. Follow this ultimate blueprint for ongoing network excellence.
Learn more

Want to take on a network assessment but don't know where to start? Like any good detective, you need to do some research and ask the right questions. So get out your virtual pen and papers and get started with this network assessment questionnaire.
P.S. This Network Assessment Template can be customized based on the specific requirements of the network and the organization. By answering these questions, you can get a better understanding of the current state of your network and identify areas for improvement. It can also help you develop a roadmap for future network upgrades and improvements.
Here's a sample network assessment questionnaire that you can use to evaluate the current state of a network:
1.Network Purpose:
- What is the purpose of your network?
- What are the critical applications running on the network?
2.Network Users:
- How many users are currently using the network?
- What are their roles and responsibilities?
3.Network Devices:
- What types of network devices are connected to the network?
- What is the make and model of the devices?
4.Network Topology:
- What is the network topology?
- How are devices connected to the network?
5.Network Bandwidth:
- What is the current bandwidth of your network?
- What is the maximum bandwidth required by your network?
6.Network Traffic Load:
- What is the average traffic load on your network?
- What is the peak traffic load on your network?
7.Network Servers:
- How many servers are currently connected to the network?
- What are the roles and functions of the servers?
8.Network Storage Capacity:
- What is the current storage capacity of your network?
- What are the types of data being stored on the network?
9.Network Backup and Recovery:
- What is the current backup and disaster recovery plan in place?
- How frequently are backups performed?
10.Network Security Measures:
- What types of security measures are currently in place?
- How are security incidents and breaches handled?
11.Network Uptime:
- What is the current network uptime percentage?
- What are the common causes of network downtime?
12.Network Performance Metrics:
- What are the KPIs used to measure network performance?
- How frequently are these metrics monitored?
13.Network Maintenance and Upgrades:
- What are the current maintenance and upgrade plans for the network?
- What is the expected lifespan of network components?
14.Network Policies and Procedures:
- What are the current network policies and procedures?
- How are these policies and procedures enforced?
15.Network Access and Permissions:
- How do you manage network access and permissions for users?
- What are the authentication and authorization mechanisms in place?
16.Network Costs:
- What are the current costs associated with network operations, maintenance, and upgrades?
- How do these costs compare to industry standards and best practices?
At this point, you should have a pretty good understanding of what is going on in your network. Performing a network assessment is like being a network detective, but instead of a magnifying glass, you use advanced network performance monioring tools to uncover hidden issues and vulnerabilities.
By following the steps outlined in this article, you can become a network detective yourself and ensure that your network is secure, optimized, and running smoothly.
You should have:
- A continuous network monitoring solution
- Measurements of key network metrics
- Historical performance data
- Identification of issues in your network (you can even set up alerts for those)
- Tools to help you troubleshoot
So, put on your detective hat and start your network assessment today!
Networks may be complex. But Obkio makes network monitoring easy. Monitor, measure, pinpoint, troubleshoot, and solve network problems.
- 14-day free trial of all premium features
- Deploy in just 10 minutes
- Monitor performance in all key network locations
- Measure real-time network metrics
- Identify and troubleshoot live network problems

You can rest assured that we're not like those pushy Sellsy people - there's no catch here. We firmly believe in the excellence of our product, but if it's not the right fit for you, we understand and want what's best for you. Monitor mutliple network types, apps and services with features for:




























 Obkio Blog
Obkio Blog