Table of Contents
Table of Contents
In the fast-paced realm of IT businesses, it's easy to overlook the intricate web that powers your operations – your network infrastructure. Let's face it, most enterprises only give it the attention it deserves when something goes wrong. And by then, the issue has often snowballed into a full-blown crisis. Maybe you've been grappling with persistent performance bottlenecks, perhaps you've stumbled upon alarming security gaps within your network or the deployment of a new service doesn’t go as planned.
It's a common scenario. But fear not, because this is precisely where the importance of a Network Assessment comes into play. In this article, we'll delve into the ins and outs of assessing your network health and performance, providing you with a comprehensive reporting template.
A deep dive into the intricacies of your current network setup, a network assessment serves as the compass guiding you through the health and vitality of your digital lifelines. It's a comprehensive audit that deploys processes and scripts to scan your network's every nook and cranny. The aim?
- Unveiling potential risks
- Spotlighting anomalies
- Gathering a wealth of data on your network performance
A thorough understanding of your network's pulse, helping you make savvy decisions for your business. Whether you're grappling with existing issues, seeking opportunities for enhancement, or simply looking for a panoramic view of your network's performance, a network assessment equips you with the insights needed for strategic decision-making.
- Evaluate the eligibility of a network before migration or service deployment.
- Determine the capacity of your network to withstand the proposed changes.
- Conduct a network risk assessment in anticipation of significant alterations.
- Strategically plan your migration or deployment based on your network's existing configurations.
- Detect any potential issues that could complicate the migration or deployment process.
- Identify and address issues that may pose challenges in the future.
- Establish a network baseline and the definition of thresholds. These thresholds serve as triggers for network alerts, indicating potential issues or security breaches in the infrastructure.
But the real magic lies in the choices it empowers you to make. Consider the scenario: contemplating a migration to a new network infrastructure. It could be a shift from the traditional MPLS network to the dynamic realm of SD-WAN, or perhaps a leap from an on-premise ERP system to the nimble embrace of a cloud-based ERP solution.
Maybe you're gearing up to deploy a game-changing service, like a hosted VoIP platform, or diving into the future with the implementation of a Secure Access Service Edge (SASE) network. Network assessment reporting will empower you to proactively address issues, strategically plan migrations, and navigate the ever-evolving landscape of network technologies.
Enter the realm of strategic documentation! The network assessment template is a structured blueprint designed to illuminate the key facets when presenting the outcomes of a network assessment. Think of it as the roadmap for Managed Service Providers (MSPs), IT professionals, network admins and any other service providers, ensuring a systematic and thorough evaluation of all crucial components of their network.
This template not only acts as a safeguard against oversight but also guarantees that the findings are conveyed consistently and comprehensively.
In a world where cyber threats loom large and organizational capabilities often lag behind, the EY Global Information Security Survey (GISS) reports a staggering 87% of organizations find themselves grappling with insufficient budgets to bolster their capabilities. To add to the complexity, many of these organizations lack a clear grasp of the network topology and significance of their most critical information and network assets. It's a digital blind spot, leaving them vulnerable without adequate safeguards.
This is where the network assessment template emerges as a knight in shining armour for MSPs. Picture this: an arsenal of information lying asleep within your network, waiting to be awakened. Without proper documentation, many organizations remain in the dark about their infrastructure's standing and struggle to optimize their technologies in alignment with business goals.
In essence, the network assessment template isn't just a fancy report, it's a strategic path to well-documented, secure, and optimized network performance monitoring.
At the heart of a seamlessly executed network assessment lies the crucial step of pinpointing the foundational services and vital components steering your business objectives. These objectives range from fortifying weak network links to strategic capacity planning, gearing up for proactive troubleshooting, or simply conducting a network health check to ensure optimal returns on your current investment.
But the journey doesn't end there. For many MSPs, the assessment serves as more than just a diagnostic tool. It provides a solid foundation, empowering them to scrutinize emerging technologies with confidence. They delve into questions of value addition, exploring how these technologies can seamlessly integrate into the existing network framework and understanding the ripple effects they'll have on the environment, ultimately culminating in an enhanced user experience.


Unlock the full potential of your network assessment journey with our step-by-step process for a comprehensive understanding of your network infrastructure. Tailored specifically for MSPs, our dedicated template is your go-to resource that provides the structured framework needed to guide you through the assessment process.
Embarking on a network assessment journey without a solid plan is akin to setting sail without a compass. Preparation and thoughtful planning are the wind in your sails, providing direction, clear objectives, and a strategic game plan that ultimately shaves precious time off the assessment process.
As you gear up for your network assessment, it's crucial to have a roadmap in mind. Here are some aspects to consider:
Network Assessment Objective:
Define the “WHY” behind your network assessment. Are you aiming to unravel the mysteries of intermittent disruptions plaguing network performance? Perhaps optimization is on your agenda, or maybe you're simply conducting a preemptive health check to proactively steer your network away from potential pitfalls.
Network Assessment Expectations:
Once the objective is clear, set your expectations. Do you envision a comprehensive report detailing the current state of all network metrics? Maybe you're seeking a list of strategic recommendations, or your goal is to pinpoint the elusive cause behind a repeating network issue.
Network Assessment Method:
The 'HOW' matters. Analyzing every nook and cranny of your business manually is not just time-consuming but also a Herculean task. Fortunately, a plethora of software options exist to conduct a network assessment efficiently. Before diving in, weigh your options and choose the method that aligns best with your goals and resources.
Ready to uncover your network's secrets?
To guide your quest, we put together network assessment checklist questions to unlock the intricacies of your network. By delving into them, you not only gain insights into your network's current state but also pinpoint areas for improvement. Think of it as the first step in crafting a roadmap for a comprehensive network assessment template.
Network Purpose:
- What is the overarching purpose of your network?
- Can you identify the critical applications running on the network?
- List all ongoing projects as well as future upgrades, rollouts and planned expansions.
Network Users:
- How many users (both internal and external) currently navigate the network?
- What roles and responsibilities do these users hold?
- Define users' activities, hours of use and type of access (Internet, remote, dial-in, VPN etc.).
Network Devices:
- Identify types (Routers, Switches, Firewalls, Hubs, Gateways) and brands (Cisco, Juniper, HP, etc.) of these network devices.
- What are their locations (Data Center, Network Closet, On-premises)?
Network Infrastructure Assessment:
- Outline the network topology.
- Identify network types (WAN, LAN, Wireless) and locations (Headquarters, Branch Offices, Remote Sites).
- How are devices interconnected within the network?
Network Bandwidth:
- What is the current bandwidth of your network?
- Identify the maximum bandwidth required by your network.
Network Traffic Load:
- What's the average and peak traffic load on your network?
Network Servers:
- How many servers are presently part of the network?
- Specify the roles and functions of these servers.
Network Storage Capacity:
- Describe the current storage capacity of your network.
- What types of data find a home within this storage?
Network Backup and Recovery:
- Share details of your current backup and disaster recovery plan.
- How frequently are backups executed?
Network Security Measures:
- List existing security measures.
- What's the protocol for handling security incidents and breaches?
Network Uptime:
- What's the current network uptime percentage?
- Determine the most common causes of network downtime. How are these issues resolved?
Network Performance Metrics:
- What are the key performance indicators (KPIs) for measuring network performance?
- Document how often these metrics are under scrutiny by using tools like Network Performance Monitoring, Ping, Traceroutes and Bandwidth tests.
Network Maintenance and Upgrades:
- What plans are in place for maintenance and upgrades (both hardware and software)?
- What's the expected lifespan of network components?
Network Policies and Procedures:
- Provide insights into current network policies (Security, Usage and Access Control Policies) and procedures.
- How are these policies enforced?
- List all internal and external SLAs.
Network Access and Permissions:
- How are network access and user permissions managed?
- Detail the authentication and authorization mechanisms in play.
Network Costs:
- Break down the current costs tied to network operations, maintenance, and upgrades.
- How do these costs stack up against industry standards and best practices?
Embarking on a solo mission to conduct a network assessment template might sound like a bold move for some businesses, but the truth is, that you don't have to navigate this terrain alone.
Trying to monitoring your network infrastructure without the right network assessment tools can be not only time-consuming and lacking in detailed insights but also fraught with the risk of human error. Manual assessments often fall short, leaving you without complete visibility of what's really happening in your network.
That's where your Network Detective comes into play, and in our case, it goes by the name Obkio Network Performance Monitoring – a top-tier network assessment tool. Unlike manual assessments, which inadvertently introduce inaccuracies, Obkio provides a 360-degree view of your network with maximum precision.
Obkio is your ally in the quest for a seamlessly performing network with optimization that goes beyond the basics. Here's how:
Strategic Deployment: Network Monitoring Agents strategically positioned at key network locations act as the eyes and ears of your operation.
Constant Evaluation: Obkio doesn't just sit idle; it actively sends and monitors synthetic data packets through your network every 500 milliseconds, ensuring a real-time evaluation.
Data Collection Mastery: The Agents, working diligently, collect valuable data about your network health, providing you with a comprehensive understanding of its inner workings.
Why settle for uncertainty when you can leverage the power of Obkio's Network Monitoring?
This tool doesn't just identify performance issues, it's your proactive ally in spotting potential weaknesses that could rear their heads in the future.
Curious to witness the transformation?
Dive into Obkio's free trial, where you can conduct a no-obligation network assessment (POC). It's your chance to swiftly determine if your network is causing headaches and gather the insights needed to troubleshoot network issues effectively.

Discover how ThinkTel, a company specializing in cutting-edge hosted and on-premises services encompassing voice, video, conferencing, and data solutions for the Enterprise, Carrier, and SMB markets across Canada, utilizes Obkio's Network Performance Monitoring solution.
This strategic implementation allows ThinkTel to assess the network capabilities of clients meticulously. The focus is on determining the network's ability to support the specific demands of Real-Time Media, providing the confidence needed to seamlessly deploy Unified Communication solutions.
Problem:
For service providers like ThinkTel, ensuring success involves conducting a thorough readiness assessment of clients' network infrastructure tailored to the specific demands of Real-Time Media workloads associated with emerging services.
This crucial step is taken proactively to mitigate risks, considering the unfortunate scenario where companies invest significant time and resources in a Unified Communications deployment only to find it falls short of delivering the expected voice or video experience.
Solution:
Recognizing the importance of preparing clients for these advanced services and aiming for a seamless technology adoption experience, the ThinkTel team acknowledged the necessity of performing a network assessment. The primary goal is to gauge the capacity of a company's WAN infrastructure, ensuring it can robustly support the demands of new business communication services.
In particular, ThinkTel aimed to harness the capabilities of Obkio's solution, integrating it into their Real-Time Media Assessment. The goal was to acquire more expansive data concerning their clients' network performance, enabling them to swiftly pinpoint and resolve any potential network issues before the deployment of new Unified Communication (UC) services. Through Obkio's dedicated solution for UC Monitoring, comprehensive data on the metrics that significantly impact UC applications is made available, enhancing ThinkTel's ability to ensure a seamless and optimized experience for their clients.
Obkio empowers service providers such as ThinkTel to proactively minimize post-deployment risks by swiftly identifying issues. This proactive approach allows clients to resolve potential issues before the new service is deployed and the migration process is finalized.
Furthermore, ThinkTel's clients can continue to leverage Obkio for ongoing network performance monitoring even after deployment. This ensures that their newly implemented systems consistently operate at optimal performance levels, providing a reliable and efficient experience over time.
Learn how ThinkTel uses Obkio Network Performance Monitoring to perform a network assessment of users’ network capacity to deploy new communication services.
Learn more

Now, it's time to roll up your sleeves and dive into the heart of the matter. In this section, we'll guide you through the practical steps of assessing your network, providing you with the tools and insights needed to unravel its intricacies.
Monitoring your network is a pivotal aspect of network assessment, involving continuous surveillance of network traffic, system performance, and overall network well-being. The primary goal of network health monitoring is twofold: to pinpoint potential issues and anomalies in the network's behaviour and to collect data for in-depth analysis and performance enhancement.
Unveiling the intricacies of network monitoring involves various techniques:
Synthetic Monitoring:
Synthetic monitoring, also referred to as active or proactive monitoring, is a method for monitoring application and network performance. This technique involves simulating user activity with network resources to assess network performance and identify potential issues.
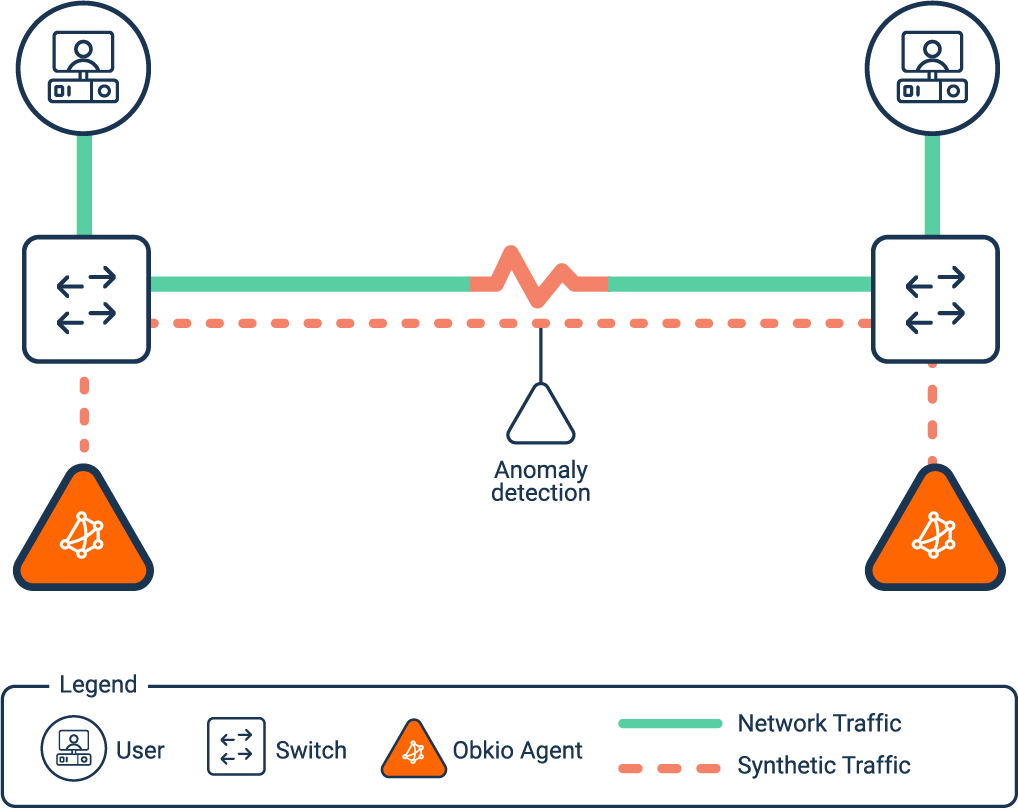
Utilizing network monitoring agents, and a synthetic Network Monitoring tool like Obkio, synthetic monitoring offers an authentic perspective from an end-user standpoint, enabling you to evaluate whether your application and network performance align with the expectations of your users.
Packet Sniffing:
This method revolves around capturing and scrutinizing the data packets traversing the network. Packet sniffers operate in real-time, offering insights into network performance, security, and user behaviour.
Network Flow Analysis:
Network flow analysis entails gathering data on traffic patterns, such as data transfer volume and frequency, and dissecting this information to identify trends and irregularities. This approach aids in recognizing potential network congestion, security threats, and other concerns.
Network Device Monitoring:
When conducting a thorough network assessment, it's imperative to scrutinize every facet of your network, encompassing critical network devices. A pivotal tool for this endeavour is the Network Device Monitoring feature embedded within Obkio's Network Monitoring Software, utilizing SNMP monitoring as a foundational element.
This feature empowers the monitoring of various network devices, including Routers, Switches, Firewalls, SD-WAN Edge Devices, and more. Its primary objective is to meticulously identify any issues potentially impacting network performance. Key parameters monitored include:
- CPU Usage
- Bandwidth Interface Errors
- Interface Errors
- Device Availability
- CRC Errors
- Interface Duplex
Through this detailed monitoring, your IT team gains the ability to swiftly detect anomalies such as short bursts of traffic (packet bursts), elevated CPU usage, bandwidth congestion, or network congestion (WAN or LAN congestion). Rapid identification of these issues facilitates pinpointing the root cause of performance challenges, enabling timely and effective resolution.
Event Log Analysis:
Event log analysis involves scrutinizing system and application logs to unearth potential issues and security threats. This technique serves as a detective, capable of detecting unauthorized access attempts, malware infections, and other security incidents.
Log types:
- Syslog
- Event Log
- Packet Capture
In essence, network monitoring emerges as an indispensable part of the network assessment template, helping to detect potential issues and security threats, and optimize overall network functionality. Utilizing a diverse set of monitoring tools and techniques, such as the Obkio Network Monitoring tool, empowers network administrators to ensure the smooth and secure operation of their networks.
A crucial aspect of obtaining a comprehensive network assessment is the analysis of historical performance data. To gain an accurate understanding of your network's performance, it is essential to scrutinize performance data over time, especially to capture intermittent issues. Historical data analysis provides a valuable context, akin to reviewing a network's performance history and evolution.
This process involves measuring key network metrics associated with performance and compiling a historical record of the collected data. By delving into historical trends, you can establish a network performance baseline, allowing you to discern patterns, anomalies, and potential bottlenecks. This baseline becomes instrumental in setting thresholds for issue alerts, helping your network management team stay ahead of potential problems.
Moreover, historical data analysis serves as a valuable tool for proactive troubleshooting. Understanding how your network has behaved over time empowers you to anticipate and address potential issues before they escalate. It's akin to having a detailed map of your network's journey, allowing you to navigate challenges with precision and foresight.
In essence, historical data analysis transforms your network assessment into a dynamic and forward-looking process, providing insights that extend beyond the present moment and into the past context of your network's performance.
Understanding your network's performance involves not only past network performance but also a focused approach to active monitoring. Following the historical data analysis, your attention shifts to extracting meaningful insights from key network metrics in real-time. These metrics serve as vital signposts in navigating the landscape of your network's health.
Here are some key metrics to use for your potential network assessment checklist:
Jitter: This metric gauges the variation in latency over time, a critical factor that can disrupt real-time applications and introduce inconsistencies in data delivery. Monitoring jitter aids in identifying areas with significant variations, allowing corrective actions to minimize its impact.
Packet Loss: Measuring the percentage of lost packets during transmission, this metric highlights potential issues arising from network congestion, hardware malfunctions, or other factors. Excessive packet loss can trigger data retransmission, adversely affecting application performance.
Latency: Assessing the delay in transmitting data packets across the network, latency is particularly crucial for real-time applications like video conferencing and VoIP (VoIP latency). Monitoring latency reveals areas of delay, enabling appropriate measures to optimize performance.
Network Throughput: This metric quantifies the amount of data transferred over the network within a specified timeframe, indicating the efficiency of data transmission and uncovering any limitations in the network infrastructure.
Bandwidth: Measuring available bandwidth assesses the network's capacity to handle expected traffic loads. This metric is instrumental in identifying bottlenecks or potential bandwidth limitations.
VoIP Quality: VoIP quality metrics evaluate the clarity, reliability, and consistency of voice communication over the network. Monitoring factors such as MOS, SNR, delay, jitter, and packet loss specific to VoIP traffic helps identify issues affecting the voice communication experience.
Error Rates: Measuring error rates encountered during data transmission, including metrics such as BER and FER, reveals potential issues with network components or environmental factors affecting data integrity.
Quality of Service (QoS): Assessing QoS effectiveness involves measuring metrics related to delay, jitter, and packet loss. This ensures the network delivers the required performance for specific applications or services.
Network Utilization: Monitoring the percentage of network capacity being utilized helps identify peak usage periods and potential bottlenecks impacting overall network performance.
Network Security: Evaluating the security posture involves measuring metrics related to firewall rules, intrusion detection systems, access control lists, and other security measures. This assessment identifies vulnerabilities and ensures the implementation of network security best practices.

Picture your network as a bustling city, humming with activity. Now, just like a city needs smooth traffic flow, your network demands seamless performance. That's where the magic of measuring key network metrics comes into play – it's like having a traffic control tower for your digital metropolis.
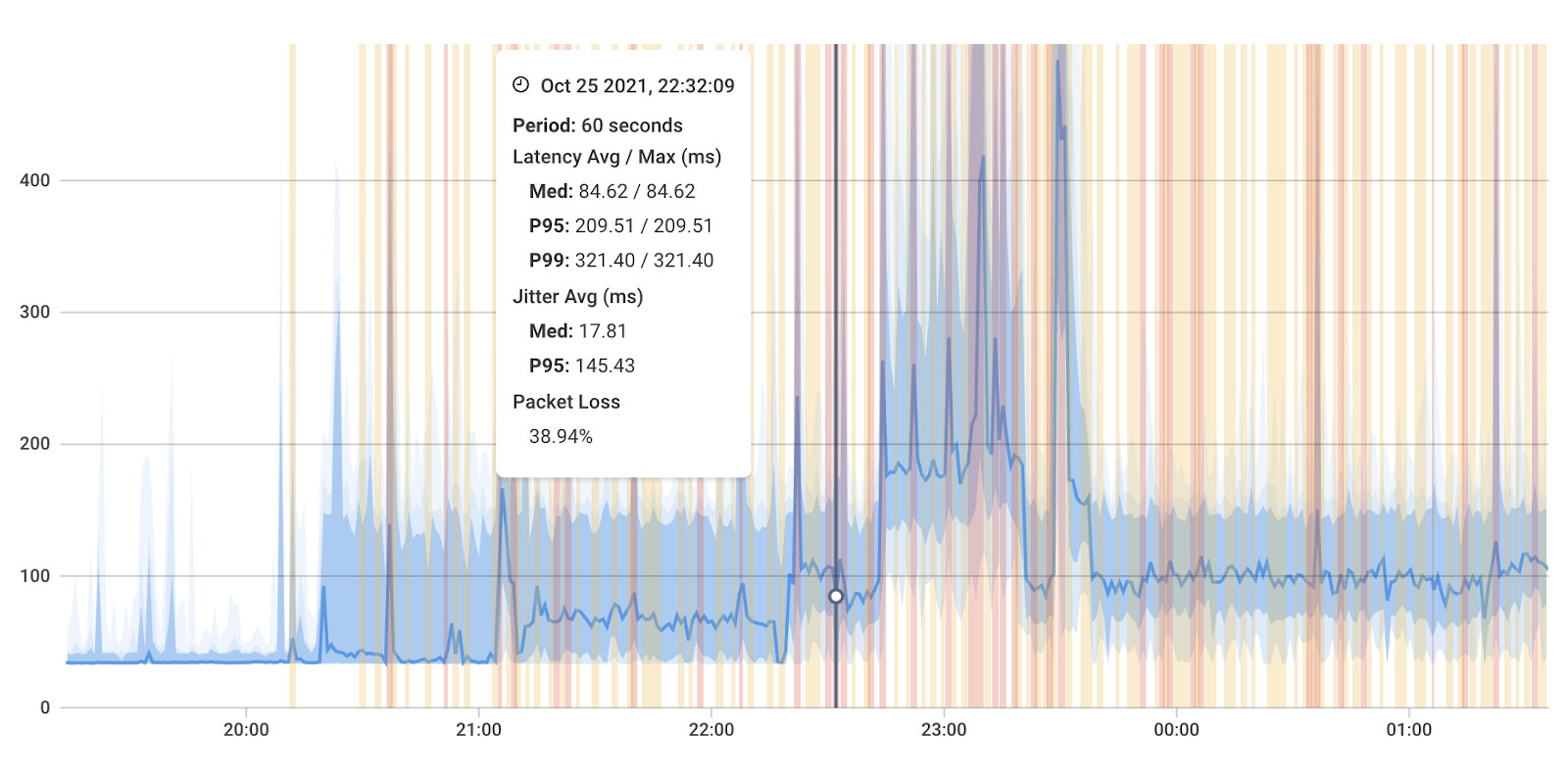
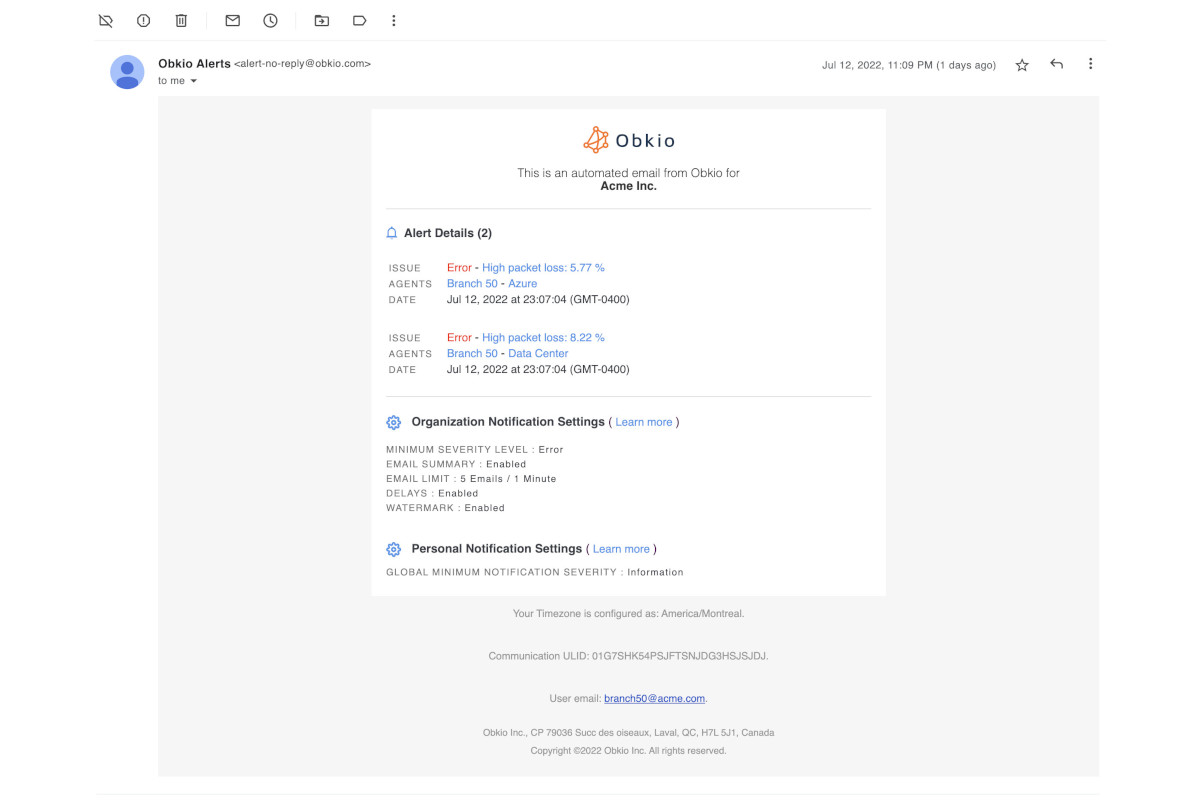
Obkio, our network superhero, swoops in with metric updates every minute, offering real-time insights. It's akin to having a radar for your network's highways, instantly spotting any potential congestion or roadblocks.
To assist you in pinpointing issues and reporting network assessment effectively, Obkio employs aggregation to reveal the most severe metric measurements. This approach sheds light on where network problems are situated and what is triggering them.
For instance, in the case of testing packet loss, the packet loss exhibited over an aggregated span of 1 hour represents the highest level of packet loss among all the brief 1-minute intervals within that hour.
This is crucial because solely presenting the average packet loss on your network might obscure intermittent network issues. By highlighting the worst-case scenarios through aggregation, Obkio’s network assessment tool ensures that potential problems don't slip through the cracks, providing a more comprehensive view of your network's health.
Learn how to measure network performance with key network metrics like throughput, latency, packet loss, jitter, packet reordering and more!
Learn more

Network mapping stands out as a valuable technique in the realm of network assessment reporting, involving the creation of a visual representation that encapsulates the components and interconnections within the network. The core objective of network mapping is to offer a lucid overview of the network's structure, allowing administrators to discern potential vulnerabilities, performance bottlenecks, and other areas in need of optimization.
The process of network mapping can take either a manual or automated route. In manual mapping, network administrators embark on a physical inspection and documentation of the network's elements and connections, encompassing routers, switches, servers, workstations, and various other devices. This method, while thorough, can be time-intensive and susceptible to errors, especially in sprawling or intricate network setups.
Once the network map takes shape, administrators leverage it as a powerful tool to pinpoint potential issues and areas that warrant optimization. This includes the identification of network bottlenecks, assessment of resource utilization, recognition of outdated hardware or software, and the unveiling of potential security vulnerabilities. In essence, network mapping emerges as a strategic compass, providing administrators with a visual aid to navigate and enhance the efficiency of their networks.
Another key technique employed in network assessment is traffic analysis, a method focused on the study and examination of network traffic. The primary goal of traffic analysis is to comprehend the flow of data within the network, pinpoint potential bottlenecks or congestion points, and identify any anomalies or security threats.
Diverse approaches exist for traffic analysis, including:
Protocol Analysis:
This method involves delving into network traffic to understand the various protocols at play, such as TCP/IP, HTTP, FTP, and SMTP. By scrutinizing protocol headers and payloads, network administrators can uncover issues like misconfigurations or malfunctions in devices, contributing to the optimization of network performance.
Network Packet Analysis:
Network packet analysis revolves around capturing and analyzing individual data/ network packets traversing the network. Through an examination of packet headers and payloads, administrators gain insights into network behaviour, performance, and security. This approach aids in the identification of unauthorized access attempts, malware infections, and other security incidents.
Flow Analysis:
Flow analysis entails the monitoring of network traffic patterns, encompassing factors like volume and frequency of data transfers. By analyzing these patterns, network administrators can detect potential network congestion, performance hurdles, or other anomalies that may necessitate optimization.
Traffic analysis can be executed through manual methods or by leveraging automated tools such as network packet analyzers or flow monitoring tools. These tools empower administrators to capture and analyze network traffic in real-time, simplifying the detection and response to potential issues or security threats.
Another critical technique in the realm of network assessment is Vulnerability Scanning, a method dedicated to identifying potential vulnerabilities within network devices, systems, and applications. The primary objective of vulnerability scanning is to proactively pinpoint potential security threats and implement appropriate measures to neutralize them before they become exploitable.
Typically executed through automated tools, vulnerability scanning involves scanning network devices, systems, and applications for known vulnerabilities. These tools rely on a comprehensive database of known vulnerabilities, coupled with testing scripts, to scrutinize network devices such as routers, switches, firewalls, and servers, as well as software applications like web applications and operating systems.
Upon the completion of the vulnerability scan, the scanning tool generates a detailed report. This report serves as a roadmap for network administrators, highlighting potential vulnerabilities and offering recommendations for effective mitigation. Armed with this information, administrators can prioritize and strategize remediation efforts based on the severity of the vulnerabilities and their potential impact on network security.
Performance testing, a pivotal technique within network assessment, delves into evaluating the network's capabilities under diverse conditions, such as heavy traffic or high network loads. The overarching goal of network testing is to unearth potential bottlenecks in performance and fine-tune the network for enhanced reliability and efficiency.
This technique encompasses various testing approaches, including:
Load Testing:
Load testing revolves around simulating scenarios of heavy traffic or high network loads to assess the network's adeptness in handling such conditions. It aids in identifying bottlenecks like slow response times or dropped packets, empowering network administrators to optimize overall network performance.
Stress Testing:
Stress testing focuses on assessing the network's resilience under extreme conditions, such as sudden spikes in traffic or potential denial-of-service (DoS) attacks. By subjecting the network to stress, administrators can pinpoint vulnerabilities and prepare for potential security incidents effectively.
Bandwidth Testing:
Bandwidth testing involves gauging the network's available bandwidth and pinpointing potential bottlenecks or congestion points. This approach assists administrators in optimizing network performance and ensuring that the network operates at its maximum capacity.
Performance testing can be executed through manual methods or automated tools. Automated performance testing tools empower network administrators to replicate diverse network conditions and measure essential performance metrics, including response times, throughput, and packet loss. These tools also generate comprehensive reports, identifying potential performance issues and furnishing recommendations for optimizing network performance.
Security testing takes center stage as a crucial part of the network assessment template, aiming to scrutinize the network's security posture and uncover potential vulnerabilities and security threats. The primary objective of security testing is to proactively identify security risks and implement necessary measures to thwart cybercriminal exploitation.
Various techniques are employed in security testing, including:
Penetration Testing:
Penetration testing involves emulating a real-world attack on the network to unveil potential vulnerabilities and security threats. Testers deploy an array of tools and techniques, such as exploiting known vulnerabilities or employing social engineering tactics, to simulate attacks and gain insights into the network's security resilience.
Vulnerability Scanning:
Vulnerability scanning entails a thorough scan of the network for known vulnerabilities, accompanied by recommendations for mitigation. Leveraging a database of known vulnerabilities and testing scripts, these tools identify potential vulnerabilities in network devices and software applications.
Threat Modeling:
Threat modelling entails a meticulous analysis of the network's architecture to identify potential security threats and vulnerabilities. This approach aids network administrators in comprehending the network's security stance and developing effective strategies to mitigate potential security risks.
Compliance Testing:
Compliance testing focuses on evaluating the network's adherence to industry regulations and standards, such as HIPAA or PCI-DSS. By conducting compliance testing, administrators can pinpoint potential issues and ensure alignment with regulatory requirements.
Following the completion of the network assessment template, a comprehensive report is generated, summarizing the findings and providing recommendations for addressing identified issues or weaknesses. This report serves as a valuable resource, offering insights on optimizing network performance, enhancing security measures, and fortifying the network's capacity to handle future growth.
Learn how to perform network testing using Network Monitoring tools to test network performance, and identify network bugs and issues.
Learn more

In this final phase, we compile the ultimate network assessment report template, drawing insights from the analysis, findings, and recommendations. The report aims to furnish a thorough snapshot of the network assessment, encompassing identified networks, hardware and software components, performance metrics, security measures, policies, and proposed enhancements.
It’s beneficial to further categorize all recommendations into different priorities (low, medium and high priority) or severity levels. This strategic step aims to streamline the implementation process, ensuring that the most critical concerns are promptly addressed.
Consider to break all improvements into these 3 groups:
- Hardware Changes
- Software Changes
- Security Changes
By prioritizing recommendations based on severity and origin, MSPs can enhance the efficiency of their network assessment efforts and swiftly attend to the most vital aspects of improvement.
Utilizing the data gathered through Obkio's app, you can conclude your Network Assessment by generating Network Performance Reports. Utilize Report Schedules to automate the execution and generation of reports on a daily, weekly, or monthly basis. These reports offer an executive summary of your network's performance health, highlighting any identified issues.
Accessible Data:
The network reporting feature enables the collection and analysis of specific network performance data presented in an easily digestible and shareable format.
Internal Data Sharing:
Obkio's network performance reports serve as valuable resources for internal use, allowing teams to gain crucial, actionable insights and make prompt decisions following the network assessment.
External Data Sharing:
When tackling network issues with your Service Provider, providing comprehensive information is key for swift escalation beyond Level 1 Support. When initiating a support ticket, utilize and generate reports to share with your Service Provider.
Informed Decision-Making:
Leveraging a network performance report facilitates quick and informed decisions concerning network optimization and health. The report draws from both current and historical network performance data and metrics.
Proactive Network Optimization:
By scrutinizing network reports and observing capacity usage trends, you can potentially forecast, detect, diagnose, and troubleshoot network issues before they escalate into complete network outages.
SLA Agreement Monitoring:
The network assessment template plays a crucial role in monitoring compliance with SLAs or service-level agreements. Use gathered information to demonstrate adherence to service or Internet SLAs or, conversely, to present evidence to your Service Provider if they are not complying with the agreed-upon service-level agreement.
Congratulations! You've successfully conducted a thorough network assessment, pinpointed areas for improvement, and implemented changes to enhance your network's performance. But the journey to optimal network health doesn't end with the assessment – it's an ongoing commitment.
The changes and recommendations derived from your network assessment are the seeds of progress. To witness them blossom into lasting improvements, consistent monitoring is paramount. Employing network monitoring tools and techniques allows you to track the implementation of changes, ensuring they are applied correctly and have the intended impact on performance.
Consider network assessments as routine check-ups for your digital infrastructure. Regular monitoring, ideally scheduled every 6 months or annually, helps you stay ahead of potential issues, adapt to evolving business objectives, and accommodate network growth. Think of it as preventive care for your network's well-being.
In the dynamic landscape of technology, change is inevitable. Every significant change in your network – whether it's scaling up operations, adopting new technologies/services, or restructuring configurations – should trigger a fresh network assessment. This proactive approach ensures that your network aligns with the evolving needs of your business and remains resilient in the face of technological advancements.
The roadmap you've followed in this article involves crucial steps, each contributing to the creation of a holistic template for continuous network assessment. Consider this comprehensive template not just as a static document but as a living, breathing guide for the continuous enhancement of your network's performance.
As you revisit this template regularly, conduct assessments, and adapt to the evolving needs of your business, you're fostering a network ecosystem that thrives today, remains agile and is prepared for the opportunities of tomorrow.
Start Your Network Assessment Today!
Unlock the full potential of your network infrastructure by embarking on a comprehensive network assessment with Obkio's state-of-the-art Monitoring Tool. Obkio’s detailed network assessment goes beyond conventional monitoring, providing you with in-depth insights into every facet of your network's performance.

- Real-time Visibility: Gain instant insights into your network's health with real-time monitoring.
- Proactive Issue Detection: Identify and resolve potential bottlenecks before they impact your users.
- Granular Analysis: Understand your network at a granular level with detailed insights into traffic patterns, latency, and bandwidth utilization.
- Identify Vulnerabilities: Pinpoint vulnerabilities and potential bottlenecks that may be hindering your network's efficiency.
- Benchmark Performance: Establish a baseline for network performance, enabling you to set and achieve optimized connectivity standards.
- Actionable Recommendations: Receive actionable recommendations based on assessment results, empowering you to proactively address issues and enhance your network's performance.

Happy networking!




























 Obkio Blog
Obkio Blog