Table of Contents
Table of Contents
We've all heard the buzz about SASE (Secure Access Service Edge) and how it's revolutionizing the way we handle network security and connectivity. But let's face it, keeping your SASE architecture running like a well-oiled machine isn't a walk in the park. It's more like a continuous sprint, with multiple moving parts, countless devices, and the never-ending quest for optimal performance.
Today, we're delving into the art and science of SASE monitoring. We'll show you how to keep your SASE architecture on the fast track, armed with the tools and insights you need to steer it through the maze of digital complexities.
So, without further ado, let's delve into the intricacies of SASE monitoring and optimization.
In the ever-accelerating realm of IT, acronyms and buzzwords can come and go faster than you can say "network security." However, one term that has remained firmly entrenched in the lexicon of modern technology is SASE, or Secure Access Service Edge. It's not just a buzzword; it's a transformative framework that's altering the way we think about network security and connectivity.
SASE, or Secure Access Service Edge, is more than just another tech acronym. It represents a seismic shift in the way organizations approach network architecture.
At its core, SASE converges network security and wide-area networking (WAN) capabilities into a cloud-native, edge-based architecture. This means that your network and security functions are no longer confined to a traditional data center but are distributed to the edge of your network. In simpler terms, SASE is about bringing network security and connectivity closer to the end-users, wherever they may be, whether in the office, at home, or on the go.
As the adoption of SASE continues to gain momentum, SASE monitoring has become more important than ever. In this ever-connected digital landscape, where remote work is the new norm and threats are increasingly sophisticated, SASE monitoring serves as the vigilant guardian of your network's health and security.
Effective SASE monitoring is your radar in the storm, providing real-time insights into the performance, security, and integrity of your SASE architecture. It helps you identify and resolve issues before they can escalate, ensuring seamless connectivity, optimal user experiences, and proactive threat mitigation.
In this blog post, we'll guide you through the intricacies of SASE monitoring, from understanding the core metrics to selecting the right tools and implementing best practices. We'll show you how SASE monitoring can be the linchpin of your IT strategy, enhancing your organization's agility, security, and overall efficiency.
The impact of SASE on network security and connectivity cannot be overstated. In an environment where remote work, cloud adoption, and an increasingly mobile workforce are the new normal, SASE addresses the critical need for a dynamic, secure, and flexible network.
SASE reshapes network security by decentralizing and distributing security measures closer to the end-users. With this approach, security is applied wherever users connect, ensuring consistent protection and minimizing latency. It provides a more effective defence against modern cyber threats, as it allows organizations to react swiftly to emerging risks.
Moreover, SASE redefines connectivity by leveraging Software-Defined Wide Area Networking (SD-WAN) capabilities. This ensures efficient, cost-effective routing of network traffic, regardless of the geographical location of the users and resources. It optimizes network performance and enhances the user experience.
In summary, SASE is not merely a buzzword; it's a paradigm shift in how organizations approach network security and connectivity. It equips IT professionals with the tools and strategies to navigate the complexities of the modern IT landscape while ensuring the integrity and security of network resources. As we delve deeper into the subsequent chapters, we'll uncover the practical aspects of SASE, from monitoring and optimizing to future trends in this transformative framework.


In an era where the digital landscape is marked by its incessant transformation, the Secure Access Service Edge (SASE) framework has emerged as a revolutionary force in network architecture and security. Understanding the fundamental principles of SASE and its transformative impact is essential for any IT professional navigating the complex seas of modern IT.
SASE is not just a simple concept; it's a holistic reimagining of how we secure and manage network access. At its core, SASE unifies network security and wide-area networking (WAN) into a singular, cloud-native architecture that extends security measures to the very edge of the network. This approach ensures that security and connectivity are no longer confined to traditional data centers but are instead delivered wherever users, applications, and data are located.
SASE integrates various critical components, such as network security, WAN, cloud-native architecture, identity and access management, and the zero-trust model. The goal is to create an agile, scalable, and secure network that adapts seamlessly to the demands of today's digital world.
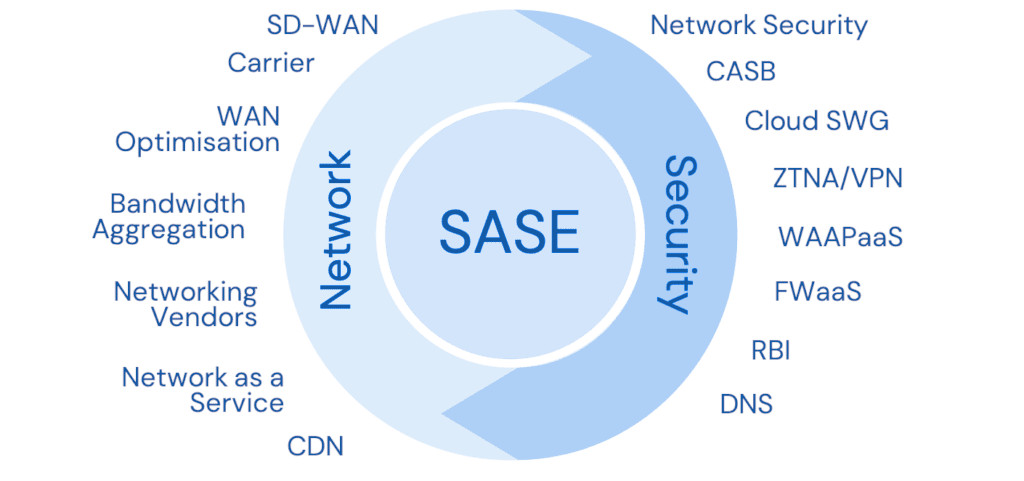
To understand the Secure Access Service Edge (SASE) framework, it's crucial to dissect its core components. SASE is a multifaceted approach to network security and connectivity, designed to meet the demands of a rapidly evolving digital landscape.
We’re going to explore the five key components that form the bedrock of SASE, delving into their functions and how they work together to create a dynamic and secure network environment. These components serve as the building blocks of a SASE architecture that ensures scalable, efficient, and highly secure access to your organization's resources, regardless of location or device.
The Secure Access Service Edge (SASE) framework typically comprises five key components:
1. Network Security:
This component includes security measures such as firewall, intrusion detection and prevention systems, data loss prevention, and secure web gateways. SASE integrates and optimizes these security functions to protect the network, regardless of the location or device being used to access it.
2. Wide Area Networking (WAN):
SASE involves WAN capabilities, such as SD-WAN (Software-Defined Wide Area Network), which enables efficient and flexible routing of network traffic. This component ensures that network traffic flows smoothly, taking the most efficient path to its destination.
3. Cloud-Native Architecture:
SASE leverages a cloud-native architecture, allowing for scalability, flexibility, and agility. With this component, organizations can easily adapt and scale their network and security services as needed without the constraints of physical hardware.
4. Identity and Access Management (IAM):
IAM is central to the SASE framework, ensuring that users and devices are authenticated and authorized appropriately before accessing network resources. This component plays a vital role in enforcing security policies and controlling access to applications and data.
5. Zero Trust Network Access (ZTNA):
Zero Trust is a foundational principle of SASE. It assumes that no entity, whether inside or outside the network, can be trusted by default. ZTNA, a key component of SASE, enforces the principle of least privilege and ensures that access is granted based on verification of the identity and security posture of users and devices.
These five components work together to create a unified, cloud-based, and secure network architecture that adapts to the modern IT landscape, where remote work and distributed resources are increasingly common. SASE provides a holistic approach to network security and connectivity, aligning with the changing needs of organizations in a digital world.
In a typical SASE architecture, when a user or device seeks access to a network or an application, it goes through the following steps:
- Authentication: Users and devices are authenticated to ensure they are who they claim to be. This is the starting point for Zero Trust security.
- Authorization: Based on the user's identity and the required resources, the system authorizes access to specific network resources and applications.
- Traffic Routing: SD-WAN technology is used to intelligently route traffic through the most efficient path to improve performance and reduce latency.
- Security Services: Network traffic passes through integrated cloud-based security services that inspect and protect against threats, malware, and unauthorized access.
- Content Filtering: Services like SWG filter and monitor web traffic, ensuring safe and secure browsing for users.
- Secure Access: Finally, authorized users and devices gain secure access to network resources and applications, while any threats or unauthorized access attempts are blocked.
The SASE is a holistic solution that addresses the changing landscape of network and security needs. It provides a flexible, secure, and efficient architecture that enables organizations to adapt to the demands of the modern digital era while ensuring the integrity and reliability of network operations.
The SASE network is designed to meet the evolving needs of organizations in the digital age, where traditional network perimeters have become increasingly obsolete, and remote and cloud-based operations are the norm.
Key Components of the SASE Network:
- Cloud-Based Architecture: At the core of the SASE network is the concept of shifting network and security services to the cloud. This cloud-based approach allows organizations to access network resources and security services from anywhere, making it highly flexible and scalable.
- Zero Trust Security: SASE follows the Zero Trust security model, which means trust is never assumed by default, regardless of the user's location. Access to network resources and applications is granted based on strict authentication and authorization, minimizing security risks.
- Software-Defined Wide Area Network (SD-WAN): SASE often incorporates SD-WAN technology, which optimizes network traffic and connectivity by dynamically routing traffic across the most efficient paths. This improves application performance and minimizes latency.
- Integrated Security Services: SASE integrates a range of security services, including firewall as a service (FWaaS), secure web gateways (SWG), data loss prevention (DLP), threat detection, and more. These services are usually supplibed by MSSPs, delivered from the cloud and offer consistent, always-on protection.
- Edge Connectivity: The SASE network can be accessed from the edge of the network, allowing remote and branch offices, mobile users, and IoT devices to connect securely and seamlessly. This means that users, wherever they are located, enjoy consistent network and security services.
- Consolidated Architecture: SASE simplifies the network and security architecture by consolidating services into a single cloud-based framework. This not only reduces complexity but also lowers operational costs.
Monitoring your SASE architecture doesn't have to be a daunting task. With the right tools, you can gain real-time insights, streamline network security, and optimize connectivity with ease. That's where Obkio's Network Monitoring tool steps in as your trusted partner.
Introducing Obkio: Your SASE Monitoring Companion
Obkio is a leading name in the world of network monitoring, renowned for its cutting-edge technology and user-centric approach. With Obkio, you can supercharge your SASE monitoring efforts to ensure your network remains secure, efficient, and agile.
Obkio empowers you to:
- Gain Unparalleled Visibility: Monitor your network performance and SASE infrastructure from end to end, ensuring every component is performing at its best.
- Proactive Issue Resolution: Identify and address network anomalies before they impact user experiences or compromise security.
- Cloud-Native Agility: Leverage the power of the cloud-native architecture to scale and adapt your monitoring capabilities to meet your evolving needs.
- User-Centric Insights: Ensure your remote and on-site users have fast, secure access to your network resources with Obkio's user-centric focus.
Unlock the potential of SASE monitoring with Obkio's Network Monitoring tool. Take the first step towards a safer, more efficient network environment. Get started today, and experience SASE monitoring at its finest.

As the digital world keeps changing, and the line between the office and the virtual world gets blurrier, keeping an eye on your Secure Access Service Edge (SASE) setup isn't just a "nice to have" anymore; it's an absolute must-do. In this chapter, we're going to dig into the nuts and bolts of SASE monitoring.
We'll break down what it is, why it's awesome, and why it's the secret sauce that can make or break your SASE game
SASE Monitoring, simply put, is the continuous oversight and assessment of your SASE architecture. It involves the vigilant surveillance of the various components that make up your SASE framework, including network security, WAN capabilities, cloud-native infrastructure, identity and access management, and more. The objective is to ensure that everything is functioning optimally, in sync, and in line with your security and performance standards.
Monitoring your SASE infrastructure isn't just a box to tick on your IT to-do list; it's a strategic move that can yield a range of significant advantages. Here are some key benefits:
- Proactive Issue Resolution: SASE monitoring allows you to spot potential problems before they escalate, keeping your network resilient and minimizing downtime.
- Enhanced Security: By continuously monitoring, you can detect and respond to security threats swiftly, protecting your organization from vulnerabilities and attacks.
- Improved User Experience: SASE monitoring ensures that your users have seamless access to network resources, no matter where they're located.
- Performance Optimization: You can fine-tune your network's performance based on real data, guaranteeing a smoother, more efficient operation.
- Cost-Efficiency: Monitoring helps you identify and eliminate unnecessary expenses, leading to cost savings.
Monitoring is the vigilant guardian of your Secure Access Service Edge (SASE) architecture. To keep your network secure, efficient, and adaptable, you need to keep a close eye on various critical components and aspects. From network traffic and security to user behavior and cost analysis, we'll navigate the vital elements that demand your attention.
In a Secure Access Service Edge (SASE) architecture, there are several key components and aspects that you should monitor to ensure its security, performance, and overall functionality. Here's a list of what you should monitor in a SASE architecture:
- Network Traffic and Bandwidth: Monitor the volume and patterns of network traffic to ensure it's within expected parameters. Identify bandwidth bottlenecks and potential overloads.
- Latency and Packet Loss: Keep an eye on network latency and packet loss rates. High latency or excessive packet loss can degrade the user experience.
- Network Security: Continuously monitor security events, intrusion attempts, and firewall activity to detect and respond to threats in real-time.
- Identity and Access Control: Monitor user and device access, ensuring that only authorized entities gain entry. Track user authentication and access behavior.
- Application Performance: Assess the performance of applications running over the network, including latency, responsiveness, and any anomalies affecting user experience.
- Zero Trust Network Access (ZTNA) Metrics: Track the effectiveness of your ZTNA implementation. Ensure that access controls are working as intended.
- VPN and Remote Access Connections: Monitor the health and performance of VPN connections, especially when dealing with remote or mobile users.
- Cloud Services Connectivity: Keep tabs on the connectivity and performance of cloud-based applications and services accessed through your SASE architecture.
- Data Loss Prevention (DLP): Set up monitoring for data loss prevention to identify and mitigate any unauthorized data transfers.
- User Behaviour Analysis: Analyze user behaviour for unusual or suspicious activities that might indicate a security breach.
- Compliance and Policy Adherence: Ensure that your SASE architecture is in compliance with industry regulations and internal policies. Monitor for any policy violations.
- Hardware and Infrastructure Health: Monitor the health of SASE components, including routers, switches, and servers, to prevent hardware failures and network downtime.
- Geographical Performance: Assess the performance of your SASE architecture across different geographical locations to identify regional variations in connectivity and security.
- Incident Response: Set up monitoring for security incidents and automate responses to minimize the impact of security breaches.
- User Experience: Use synthetic transaction monitoring to gauge the end-user experience, ensuring that applications perform as expected and users have a seamless experience.
- Scalability and Capacity Planning: Monitor resource utilization to plan for scaling your SASE architecture as your organization's needs evolve.
Effective monitoring across these aspects will help you maintain a secure, efficient, and resilient SASE architecture that meets the needs of your organization and its users. It also enables proactive issue resolution and improved network performance.
Learn how to monitor SD-WAN networks with Network Monitoring to get complete visibility over your SD-WAN service and identify SD-WAN issues.
Learn more

Neglecting SASE monitoring can have dire consequences. The risks include:
- Security Vulnerabilities: Unmonitored SASE architecture is susceptible to security breaches and data theft.
- Performance Bottlenecks: Without monitoring, you might miss performance issues that can lead to network congestion and slowdowns.
- Cost Overruns: Unexpected network issues can result in unbudgeted costs.
- Operational Inefficiencies: Neglecting monitoring can lead to poor resource allocation and inefficiencies in the network.
In summary, SASE monitoring is the linchpin of a robust, secure, and high-performing network. It safeguards your organization from risks, enhances performance, and ensures that you make the most of your SASE investment.
In the chapters that follow, we'll delve deeper into the practical aspects of SASE monitoring, offering insights and guidance to help you navigate the challenges and harness the benefits.
SASE monitoring is only as effective as the tools and solutions you employ and it isn't a one-size-fits-all game. In this chapter, we're diving headfirst into the ocean of monitoring solutions, getting cozy with what's out there, and discussing the upsides and downsides of each.
SASE monitoring tools are like the superheroes of your network, each with its own unique superpowers. Let's meet some of them:
1. SASE Monitoring with Network Performance Monitoring (NPM) Tools: Ensuring Your Network's Peak Performance
Your SASE architecture is the backbone of your organization's connectivity and security. Ensuring it performs at its best is paramount, and that's where Network Performance Monitoring (NPM) tools come into play.
NPM tools are the diligent observers and fitness trainers for your network, making sure it's always running at its peak. These tools specialize in keeping a watchful eye on network speed, bandwidth utilization, packet loss, and more.
Just as a personal fitness trainer tailors workouts to maintain your physical health, NPM tools optimize your network's health, ensuring it can handle your data-intensive workouts (read: tasks) without breaking a sweat.
Choose your Ultimate Fighter: Network Performance Monitoring tool to ensure optimal network performance. Learn about the types of tools, features & uses.
Learn more

1. Speed and Bandwidth:
First and foremost, NPM tools are like your network's speedometers. They keep a constant eye on how fast data travels across your network by monitoring network speed and bandwidth. When data moves sluggishly, they'll be the first to notice. Whether it's a sudden drop in download speeds when you're streaming your favourite show or a laggy video conference call, NPM tools are on the lookout to spot network slowdowns and bottlenecks.
2. Bandwidth Utilization:
Think of bandwidth utilization as the diet plan for your network. NPM tools keep tabs on how much data is being consumed at any given moment. They'll let you know if your network is on a data diet, consuming too much, or maintaining a healthy balance. This is crucial for ensuring that your network resources are efficiently allocated and that you're not overpaying for bandwidth you don't need.
3. Packet Loss:
NPM tools also watch out for packet loss, which can be equated to your network's "stamina." When data packets get dropped during transmission, it's like your network is losing its breath. Packet loss can lead to data retransmissions and sluggish performance. These tools act as the network's stamina trainers, ensuring it can go the distance without huffing and puffing.
4. Real-time Monitoring:
Much like a personal fitness trainer who's always by your side during a workout, NPM tools provide real-time monitoring. They're there to alert you the moment something goes awry in your network, so you can take immediate action to resolve issues.
In a SASE architecture, these NPM tools play a vital role in maintaining the overall health of your network. They provide crucial insights into network performance, allowing you to detect and address issues swiftly. By ensuring that your network is running at its best, NPM tools help guarantee a smooth and efficient experience for your users, just like a dedicated fitness trainer keeps you in top physical shape.
- Superpowers: NPM tools are all about speed, bandwidth, and data movement. They excel at optimizing network performance and ensuring efficient data transfer, making them ideal for organizations focused on network speed.
- Kryptonite: However, they might not be the best at identifying security threats.
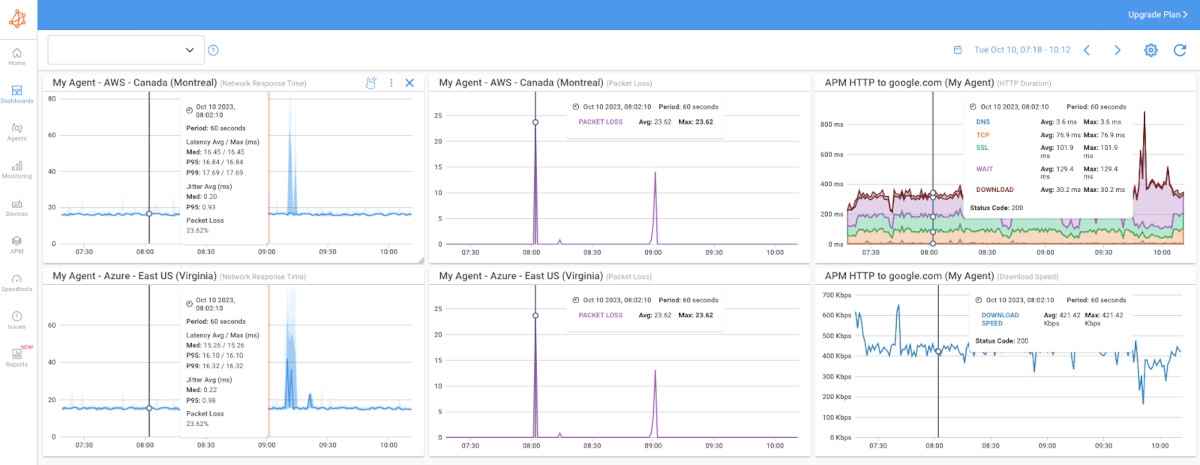
Among the multitude of NPM solutions available, Obkio's Network Performance Monitoring tool distinguishes itself with its user-centric approach and real-time insights.
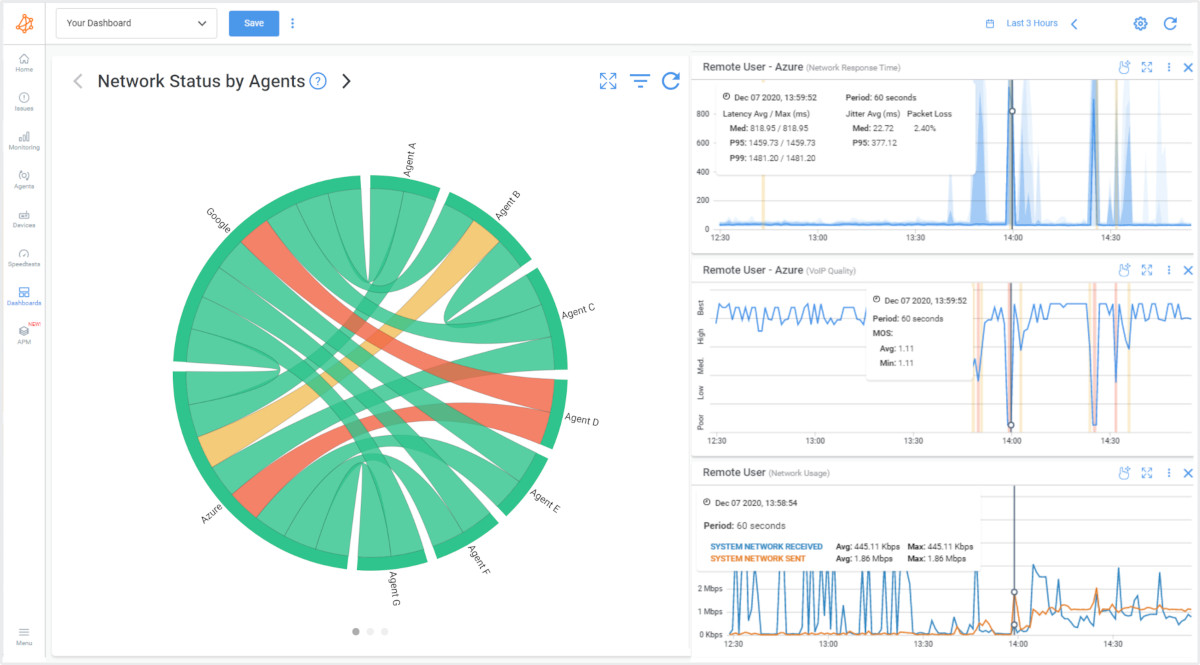
- User-Centric Focus: Obkio's NPM tool prioritizes the user experience. It provides insights into how network performance impacts your end-users, ensuring that they have a seamless and frustration-free experience.
- Real-Time Monitoring: Like a vigilant trainer, Obkio's tool doesn't wait for the end of the month to report on your network's health. It provides real-time data, allowing you to take immediate action when network issues arise.
- Comprehensive Network Visibility: Obkio's solution offers in-depth visibility into network performance metrics, helping you identify and address issues affecting speed, bandwidth utilization, and packet loss.
- Network Device Monitoring: On top of NPM capabilities, Obkio's tool includes network device monitoring, providing insights into the health and performance of your network devices.
- Application Performance Monitoring (APM): Obkio's APM features ensure that you can keep a close eye on the performance of the applications running on your network, delivering a holistic view of network and application performance.
- Ease of Implementation: It's easy to get started with Obkio's NPM tool, making it accessible for organizations of all sizes.
- Scalability: Whether you're a small business or a large enterprise, Obkio's tool scales to meet your needs.
When it comes to keeping your SASE architecture in peak condition, Obkio's Network Performance Monitoring tool is your trusted partner. With a strong focus on user experience and real-time insights, it ensures that your network operates at its best, just like a dedicated fitness trainer helping you stay in top shape.

Obkio is a vendor neutral solution, so you can use it to monitor diffferent SASE services such like:
2. SASE Monitoring with Security Information and Event Management (SIEM) Solutions: Your Watchful Guardians
In the world of Secure Access Service Edge (SASE) monitoring, SIEM solutions play a pivotal role in safeguarding your SASE architecture by keeping an eagle eye on security events, analyzing logs, and detecting anomalies or potential bad actors. Just as a diligent security guard watches over your home or office, SIEM tools diligently protect your network from security threats, breaches, and suspicious activities.
1. Detecting Suspicious Activity:
SIEM solutions are the digital detectives of your network. They continuously monitor the activity across your network and compare it to established patterns and rules. If they spot any behaviour that deviates from the norm, they raise the red flag. Whether it's an unauthorized access attempt, a sudden spike in data transfers, or unusual login patterns, SIEM tools are there to alert you.
2. Analyzing Logs and Events:
Imagine logs as a trail of breadcrumbs left by every action taken on your network. SIEM solutions not only collect these logs but also analyze them in real-time. They make sense of the chaos and provide you with a coherent picture of what's happening on your network. This log analysis is crucial for identifying security incidents and understanding their scope.
3. Correlation and Context:
SIEM solutions don't just focus on individual events; they're experts at connecting the dots. They correlate events and gather context, helping you understand the bigger picture. This is essential for determining if seemingly unrelated incidents are part of a larger security threat.
4. Real-Time Alerts:
In the security world, time is of the essence. SIEM solutions provide real-time alerts when they detect any suspicious activity or threats. This immediacy allows you to respond promptly, potentially mitigating the impact of security incidents.
5. Regulatory Compliance:
SIEM tools play a critical role in maintaining regulatory compliance. They help you track and report on security events, making it easier to meet industry standards and requirements.
- Superpowers: SIEM solutions are the guardians of your network, adept at identifying and responding to security threats and anomalies in real-time. They offer top-tier security event monitoring.
- Kryptonite: While their focus is on security, they may not be as proficient at performance monitoring. SIEM solutions might not provide the comprehensive insights needed to optimize network performance or user experience.
In a SASE architecture, where security is paramount, SIEM solutions are indispensable. They act as the eyes and ears of your network, ensuring that it remains safe from external threats and internal anomalies. Their real-time monitoring, log analysis, and correlation capabilities make them the trusted guardians of your digital realm.
3. SASE Monitoring with User and Entity Behavior Analytics (UEBA) Systems: Uncovering the Behavioral Patterns
When it comes to monitoring SASE architectures, UEBA systems are great for understanding the behavioural patterns of users and entities on your network. These systems are akin to behavioural psychologists, continuously analyzing and deciphering the actions and interactions of users and entities to detect any unusual or suspicious activities. UEBA systems are the invaluable agents that keep a close eye on the behavioural spectrum of your network.
1. Behavioral Analysis:
UEBA systems specialize in behavioural analysis. They build a network baseline of what "normal" behaviour looks like for every user and entity on your network. This means they learn what is typical for each user, from the applications they use to the time they usually log in and log out.
2. Anomaly Detection:
Once they have a grasp of what's normal, UEBA systems become experts at identifying anomalies. These could be deviations from the established patterns, such as a user accessing sensitive data at an unusual time or using applications they don't typically use.
3. Insider Threat Detection:
One of the primary roles of UEBA systems is to uncover insider threats. They detect unusual behaviours that might indicate an employee or entity is acting maliciously or negligently. This could include unauthorized data access, suspicious data transfers, or changes in user privileges.
4. User Experience Enhancement:
UEBA systems are also about making the user experience better. By understanding user behaviour, they can help identify ways to streamline processes, improve application access, and ensure that users have a seamless and productive experience on the network.
5. Incident Response and Forensics:
In the event of a security incident, UEBA systems provide invaluable data for incident response and forensics. They can help investigators trace back the steps of the attacker or identify the source of a breach.
- Superpowers: UEBA systems are experts at detecting unusual user behaviours and insider threats. They're the behavioural psychologists of your network, continuously monitoring for signs of suspicious or unauthorized activities.
- Kryptonite: However, they might not cover every performance detail. If you're looking for in-depth performance monitoring, UEBA systems might not provide the complete picture you need.
UEBA systems are integral to a comprehensive SASE monitoring strategy. By focusing on behaviour, they provide a more nuanced and contextual understanding of network activities. In an era where insider threats and complex cyberattacks are prevalent, UEBA systems act as the vigilant watchers, ensuring that your network is protected, users are productive, and security is fortified.
4. SASE Monitoring with Application Performance Monitoring (APM) Solutions: Ensuring Peak Application Performance
In SASE monitoring, Application Performance Monitoring (APM) solutions take on the role of quality control experts, ensuring that your applications operate like well-oiled machines. These solutions focus on the performance and reliability of your applications, making sure they deliver a seamless and responsive user experience.
Just as a quality control team ensures that every product coming off the assembly line meets the highest standards, APM solutions guarantee the reliability and efficiency of your network's applications.

1. Performance Metrics Tracking:
APM solutions are all about numbers and metrics. They track various performance indicators such as response times, page load times, and transaction speeds. This data helps you understand how your applications are performing and where improvements may be needed.
2. User Experience Enhancement:
APM solutions are user advocates. They put the user experience front and center, making sure that your applications are responsive and deliver a smooth experience. This is crucial for keeping end-users happy and productive.
3. Anomaly Detection:
Much like a vigilant supervisor on a production line, APM solutions can detect anomalies in application behaviour. If an application suddenly starts slowing down or experiencing errors, APM tools alert you to investigate and rectify the issue promptly.
4. Transaction Monitoring:
They keep a close eye on application transactions, ensuring that processes like payments, data transfers, and user interactions run smoothly. If something goes wrong, APM solutions are there to pinpoint the problem.
5. Root Cause Analysis:
When issues arise, APM solutions provide deep insights to help you identify the root causes. They offer a comprehensive view of the application's internal workings, helping you pinpoint and resolve problems swiftly.
- Superpowers: APM solutions are all about optimizing application performance, ensuring your applications run smoothly and efficiently. They are your app's best friends, monitoring metrics like response times and page load speeds.
- Kryptonite: Their focus is on applications, not cybersecurity. APM solutions may not provide comprehensive security insights and won't be the primary tool to guard your network against cyber intruders.
In a SASE architecture, where the performance of cloud-based and on-premises applications is critical, APM solutions play a vital role in maintaining a seamless and efficient user experience. They are your quality control experts, ensuring that your applications meet the highest standards, just like a watchful supervisor on an assembly line ensuring that each product is top-notch.
Discover APM for HTTP URLs: Enhance web app performance, troubleshoot issues & delight users with powerful monitoring solutions.
Learn more

When monitoring SASE infrastructures, ZTNA monitoring tools ensure that only the right people, or entities, get access to your network. Just as diligent bouncers check IDs and maintain the guest list at a club, ZTNA tools are the gatekeepers, verifying identities, and enforcing access controls to guarantee the security of your network.
1. Identity Verification:
ZTNA tools put a strong focus on identity verification. They ensure that each user or entity attempting to access the network is who they claim to be. This is done through various authentication methods, such as multi-factor authentication (MFA), certificates, or biometrics.
2. Access Control:
Once identities are confirmed, ZTNA tools determine what each user or entity is allowed to access. They enforce access controls based on policies that have been defined by your organization. These policies can be highly granular, specifying who can access what resources.
3. Least Privilege Principle:
ZTNA tools adhere to the principle of least privilege, which means they grant users the minimum level of access necessary to perform their tasks. This reduces the risk of unauthorized access to sensitive information.
4. Continuous Monitoring:
These tools continuously monitor user and entity behavior during a session. If an established session shows unusual activity, it raises alerts or can terminate the session to prevent potential breaches.
5. Security Enforcement:
ZTNA monitoring tools not only grant access but also enforce security policies. This means they can scan traffic for malware, identify potential threats, and respond in real-time to protect the network.
- Superpowers: ZTNA tools are perfect for organizations prioritizing security. They enforce Zero Trust policies and ensure only authorized users gain access to network resources, enhancing security.
- Kryptonite: However, they might not provide a holistic view of network performance. If you're looking for comprehensive performance monitoring, ZTNA tools may have some performance constraints.
In the context of SASE, where network access is often remote, ZTNA monitoring tools are critical for maintaining security. They are the security bouncers at the entrance, ensuring that only authorized users or entities are allowed into the party while keeping potential threats at bay. By verifying identities, enforcing access controls, and continuously monitoring sessions, they provide a robust defence against unauthorized access and potential security breaches.
Cloud Monitoring Services specialize in ensuring that everything in your network's cloud environment is sunny and bright. Whether your applications and data are hosted in public or private clouds, these services keep an eye on the cloud's atmospheric conditions to prevent any unexpected storms.
Just as a weather forecaster helps you prepare for whatever Mother Nature might throw at you, cloud monitoring services ensure that your cloud-based operations are smooth, secure, and reliable.
1. Cloud Performance and Availability:
Cloud monitoring services keep tabs on the performance and availability of your cloud-based applications and services. They assess the speed, responsiveness, and overall health of cloud resources, ensuring that users experience a seamless and uninterrupted connection.
2. Resource Allocation and Optimization:
Much like a good weather forecast helps you plan your outdoor activities, cloud monitoring services assist you in optimizing your cloud resource allocation. They ensure that you're not over-provisioning or underutilizing cloud resources, helping you save costs and maintain efficiency.
3. Security in the Cloud:
Just as weather forecasters can predict incoming storms, cloud monitoring services detect potential security threats and vulnerabilities in the cloud environment. They can identify suspicious activities, unauthorized access attempts, or anomalies, enabling you to take proactive security measures.
4. Compliance and Data Protection:
Cloud monitoring services assist in maintaining regulatory compliance, which is essential in various industries. They help you track and report on cloud activities, ensuring that your data is protected and in line with industry standards and legal requirements.
5. Real-Time Alerts:
Like weather forecasters providing you with the latest updates, cloud monitoring services offer real-time alerts. They notify you of any issues or impending problems in the cloud environment, allowing you to respond swiftly.
- Superpowers: Cloud monitoring services are ideal for organizations heavily reliant on cloud resources and applications. They keep your cloud operations sunny and bright, monitoring cloud performance and availability.
- Kryptonite: They may not pay as much attention to on-premises gear. If your network is a mix of cloud and on-premises resources, you might have some blind spots in on-premises performance and security.
In the SASE landscape, where organizations increasingly rely on cloud resources and services, cloud monitoring services are indispensable. They act as your cloud weather forecasters, ensuring that everything remains sunny and bright in the cloud. By continuously monitoring cloud performance, resource allocation, security, compliance, and providing real-time network monitoring alerts, they help you navigate the ever-changing cloud environment with confidence.
In a nutshell, assembling the right mix of monitoring tools is like putting together a dream team to protect and optimize your SASE architecture. It's all about achieving a balance that aligns with your organization's specific needs.
By understanding the superpowers and limitations of each tool, you can create a tailored monitoring strategy that keeps your SASE realm safe and sound while optimizing performance and security.
Monitoring a Secure Access Service Edge (SASE) architecture can be a demanding task, presenting several challenges that IT professionals must navigate. As organizations embrace this comprehensive framework, they must grapple with the intricacies of SASE monitoring while navigating the diverse and multifaceted nature of the SASE architecture itself.
In this section, we delve into the formidable challenges IT professionals encounter when monitoring a SASE environment, where real-time visibility, diverse ecosystems, and complex policies demand vigilant attention. We'll also explore the inherent complexities of the SASE architecture, a landscape characterized by hybrid environments, Zero Trust implementation, and the dynamic workforce of today's digital age.
These challenges include:
- Diverse Ecosystems: SASE encompasses a wide range of elements, from on-premises to cloud-based services, mobile devices, and remote users. Managing and monitoring this diverse ecosystem can be complex, as each component may have different monitoring requirements.
- Real-Time Visibility: SASE requires real-time visibility into network traffic and security events. Monitoring solutions must provide timely insights to detect and respond to security threats, making real-time monitoring a necessity.
- User and Entity Behavior: Monitoring the behaviour of users and entities across the network is crucial for security. However, interpreting this behaviour and distinguishing between legitimate and malicious activities can be complex, especially with the evolving tactics of cybercriminals.
- Scalability: As organizations grow and adapt, their SASE architecture must scale to accommodate the increasing number of users and devices. Monitoring tools need to scale with the network to provide comprehensive coverage.
- Data Volume: SASE networks generate vast amounts of data. Effectively processing and analyzing this data for insights can be overwhelming without the right tools and strategies in place.
- Integration Challenges: Integrating various monitoring tools into the SASE environment can be tricky. These tools may come from different vendors and use various protocols, requiring careful planning and configuration.
The SASE architecture is inherently complex due to its comprehensive nature, combining network security and access solutions. Here are some of the complexities that IT professionals encounter:
- Hybrid Environment: SASE often operates in a hybrid environment, combining on-premises infrastructure with cloud-based services and resources. Managing the interplay between these elements while maintaining security can be challenging.
- Security Everywhere: SASE promotes a "security everywhere" approach, which requires implementing security measures at all points of network access. This includes securing remote users, branch offices, and cloud resources, which can be intricate to set up and maintain.
- Zero Trust Implementation: Implementing the Zero Trust model within SASE, which assumes that no entity, whether inside or outside the network, can be trusted by default, involves configuring strict access controls, user verification, and continuous monitoring. This approach can be complex to implement effectively.
- Regulatory Compliance: Meeting industry-specific and regional regulatory requirements while maintaining the flexibility and adaptability of SASE can be complex. Organizations must navigate a maze of compliance standards while ensuring data protection.
- Dynamic Workforce: SASE serves organizations with a dynamic workforce, which includes remote workers, mobile devices, and varying access needs. Managing access and security for this diverse group is a considerable challenge.
- Evolving Threat Landscape: The threat landscape is constantly evolving, with new types of cyberattacks and vulnerabilities emerging regularly. Keeping up with these threats and adapting security measures can be complex.
To overcome these challenges and address the complexities of SASE, organizations need a well-thought-out monitoring and security strategy, robust tools and solutions, and a commitment to staying informed about the evolving landscape of network security and access.
This comprehensive guide explores the fundamentals, benefits, and implementation of network monitoring in SaaS environments.
Learn more

As organizations embark on the journey of Secure Access Service Edge (SASE) implementation, they are confronted with a host of challenges, from managing diverse ecosystems to ensuring real-time visibility and balancing complex policies. The complexities of the SASE architecture, with its hybrid nature and the need for Zero Trust security, further compound the difficulties.
In this landscape, a comprehensive solution becomes invaluable. An end-to-end Network Performance Monitoring tool, such as Obkio, equipped with Application Performance Monitoring (APM) capabilities, offers a powerful strategy for overcoming these challenges and maximizing the potential of the SASE architecture. Here's how:
- Real-Time Visibility: Obkio provides real-time visibility into network performance, enabling organizations to detect and address issues promptly. Its APM capabilities extend this visibility to applications, ensuring that they run smoothly and efficiently.
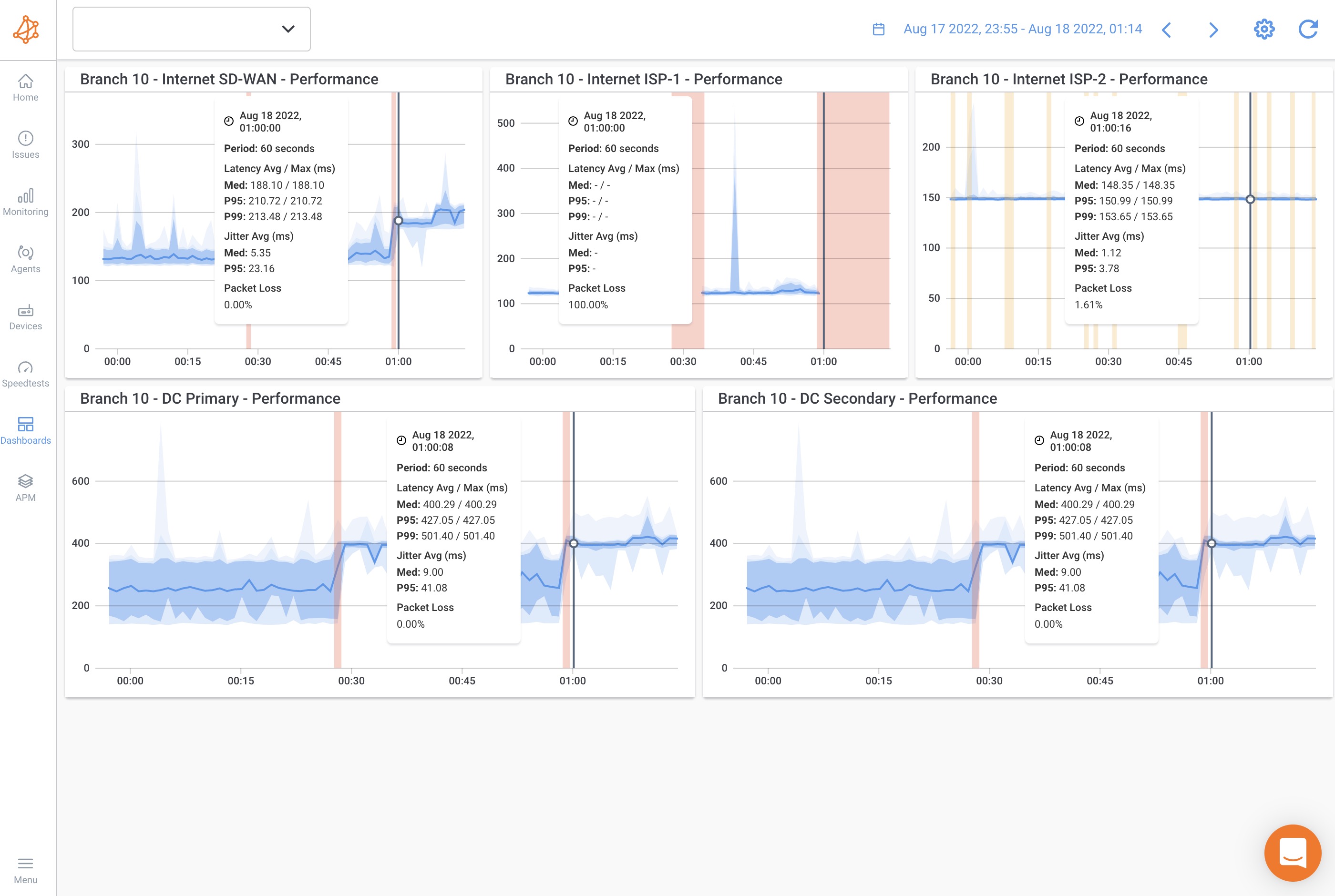
- Distributed Monitoring: Obkio's distributed monitoring architecture ensures real-time visibility into network and application performance across all locations, whether they are on-premises or in the cloud. This centralized monitoring approach enables organizations to detect and resolve issues promptly.
- Diverse Ecosystems: Obkio's flexibility and adaptability allow it to monitor a diverse range of network environments, whether on-premises or in the cloud. It ensures that all components of the SASE ecosystem are covered, offering a unified monitoring approach.
- User and Entity Behaviour: With its APM features, Obkio monitors user and entity behavior within applications, helping organizations understand how users interact with critical business tools. This behavioral analysis is invaluable for both security and performance optimization.
- Synthetic Monitoring: Obkio's synthetic monitoring capabilities offer proactive monitoring without capturing user data. This non-intrusive approach allows organizations to simulate user interactions with applications and services, identify performance issues before they impact real users, and ensure a high-quality user experience without compromising data privacy.
- Dynamic Workforce: As organizations embrace dynamic workforces, Obkio supports remote users and mobile devices, ensuring that network access remains secure and applications perform optimally. Its user-centric focus ensures a seamless experience for all users.
In summary, an end-to-end Network Performance Monitoring tool like Obkio, enriched with APM capabilities, addresses the challenges of SASE monitoring and the complexities of the SASE architecture.
By offering real-time visibility, monitoring diverse ecosystems, understanding user and entity behaviour, and supporting security everywhere, Obkio empowers organizations to navigate the SASE landscape with confidence. It allows them to assemble their monitoring Avengers, ensuring an efficient, and optimized SASE realm with 360-degree visibility at all times.
The implementation of Secure Access Service Edge (SASE) is a significant and transformative undertaking for organizations. Effectively navigating the SASE landscape requires meticulous planning and the right tools, with monitoring playing a pivotal role in its success. The same goes when you’re implementing other large network infrastructure, like MPLS to SD-WAN migrations.
Think of SASE without monitoring as setting sail on a voyage without navigation tools; it's a perilous journey with uncertain outcomes.
Certainly, let's explain why monitoring a Secure Access Service Edge (SASE) implementation is essential and when it should be conducted:
Monitoring is essential for SASE implementations for several reasons:
- Tailored Performance Optimization: SASE implementations often involve a mix of cloud resources, remote users, and security policies. Monitoring allows organizations to tailor their performance optimization efforts to this unique setup, ensuring that each component operates efficiently.
- Security Enforcement: In SASE, security is paramount. Monitoring plays a pivotal role in enforcing SASE's Zero Trust security policies by continuously monitoring network access, identifying potential security threats, and responding in real-time to protect against unauthorized access attempts.
- User Experience Assurance: A seamless user experience is a fundamental goal of SASE. Monitoring ensures that applications and services perform optimally for remote users, minimizing latency, and ensuring high availability. This user-centric approach is critical in a SASE environment.
- Policy Adherence: SASE relies on a complex web of access and security policies. Monitoring helps organizations ensure that these policies are adhered to consistently across the SASE architecture, maintaining the framework's integrity.
- Compliance Requirements: Many industries have specific compliance standards. Monitoring is vital for demonstrating compliance with these standards within the context of a SASE implementation. It provides the evidence needed to show that your SASE network meets industry-specific and regional regulatory requirements.
In a SASE implementation, monitoring is not a one-size-fits-all approach. Instead, it's a tailored strategy that ensures the efficient operation of the network, and is indispensable for achieving the goals and principles of the SASE framework within the implementation.
Monitoring in a SASE implementation should be an ongoing, continuous process. Here are some key points in time when monitoring is particularly important:
- Before Implementation: Deploy network and application monitoring before the SASE implementation begins. This early phase allows you to monitor the previous infrastructure and troubleshoot any existing issues that can affect the implementation. It's a proactive step to ensure a smooth transition to SASE.
- During Deployment: Monitoring should begin as soon as the SASE implementation is deployed. This initial phase helps in identifying any configuration issues, compatibility problems, or security gaps. It's essential to ensure that the SASE framework is set up correctly from the start.
- Day-to-Day Operations: Continuous monitoring during daily operations is essential. It provides insights into the performance and security of your network and applications, helping you address issues as they arise and optimize network operations.
- After Implementation: After the SASE implementation is complete, monitoring remains essential for continuous, real-time assessment of network performance, security, and policy enforcement.
- Scaling or Changing the Network: If you're scaling your SASE environment or making changes to your network, monitoring is vital. It ensures that the network continues to operate efficiently and securely as it grows or undergoes modifications.
- Incident Response: In the event of a security incident or network disruption, monitoring is crucial for identifying the root cause, containing the issue, and restoring normal operations.
- Compliance Audits: Regulatory compliance requires ongoing monitoring and reporting. Conduct regular audits to ensure that your network operations adhere to industry standards and legal requirements.
In summary, monitoring a SASE implementation involves a proactive phase before deployment, during, and after the implementation, as well as continuous monitoring during daily operations. It ensures the success, security, and compliance of your SASE environment and can even troubleshoot issues in the previous infrastructure before implementation.
Learn how to monitor SD-WAN migrations with Network Monitoring for complete visibility over your SD-WAN service, before, after & during migrations.
Learn more

In the world of monitoring your Secure Access Service Edge (SASE) architecture, it's kind of like keeping an eye on your network's vital signs. In this section, we’re diving into the importance of figuring out which metrics truly matter and how to make sense of them. This part of our journey is all about decoding the health of your SASE architecture.
- Latency: Latency measures the time it takes for data to travel from its source to its destination. In a SASE implementation, monitoring latency is vital as it directly impacts the user experience. High latency can result in slow application performance and, in some cases, can be a sign of network congestion.
- Bandwidth Utilization: Monitoring the bandwidth utilization provides insights into how much of your available network capacity is being used. Understanding bandwidth consumption is crucial for optimizing network resources and avoiding bottlenecks.
- Packet Loss: Packet loss indicates data packets that fail to reach their destination. High packet loss rates can disrupt network communication and adversely affect applications. Identifying and addressing packet loss is essential for a reliable network.
- Security Events: SASE's emphasis on security requires monitoring security events and incidents. These include unauthorized access attempts, malware detections, and other threats. Monitoring security events helps maintain a strong security posture and ensures that Zero Trust policies are effectively enforced.
- Application Performance Metrics: Application-level metrics such as response times, page load speeds, and transaction completion rates are crucial for ensuring that critical business applications perform optimally. These metrics directly impact the user experience.
- User and Entity Behavior: Monitoring user and entity behaviour involves tracking activities and access patterns. Unusual behaviour or deviations from established norms can signal potential security issues, making this metric essential for threat detection.
Interpreting these metrics effectively is essential for gauging the health of your SASE architecture:
Step 1. Baseline Comparison:
Comparing current metrics to historical data or established baselines helps identify anomalies. Significant deviations from baseline values can signal issues that require attention.
Step 2. Correlation Analysis:
Correlating different metrics can reveal insights that individual metrics may not provide. For example, correlating latency and packet loss may help pinpoint network congestion as the cause of latency issues.
Step 3. Threshold Alerts:
Set threshold alerts for each metric to trigger notifications when certain thresholds are breached. This proactive approach allows you to address issues as they arise, reducing downtime and security risks.
Step 4. User Experience Impact:
Consider how metrics impact the user experience. If latency is high or application performance metrics are poor, it directly affects how users perceive your network's health. Monitor these metrics closely to ensure a positive user experience.
Step 5. Pattern Recognition:
Look for recurring patterns in metrics. Identifying consistent patterns can help predict and prevent issues. For instance, recurring security events in a specific location may indicate a potential security threat that requires further investigation.
By understanding the crucial metrics for SASE monitoring and employing effective interpretation methods, organizations can gauge the health of their SASE architecture accurately. This knowledge empowers IT teams to proactively optimize performance, enhance security, and maintain a reliable and secure SASE environment.
A SASE environment, while transformative, is not immune to challenges. SASE monitoring is your vigilant sentinel, standing guard to identify and address issues promptly.
SASE monitoring tools are essential for detecting and troubleshooting these issues, ensuring a reliable and secure network environment. Monitoring solutions offer the insights and data needed to address these challenges promptly, optimizing performance and maintaining security.
Here's what SASE issues you need to look out for, and how you can troubleshoot:
- High Latency: Delay in data transmission, resulting in slow application performance and a poor user experience. This can occur due to network congestion, inefficient routing, or excessive packet processing.
- Bandwidth Saturation: When network bandwidth is fully utilized or exceeded, it leads to slowdowns, packet loss, and decreased application performance. This can happen in scenarios with high data transfer requirements.
- Packet Loss: The loss of data packets during transmission can result from network congestion, hardware failures, or faulty configurations. Packet loss negatively impacts real-time applications like VoIP and video conferencing.
- Application Bottlenecks: Some applications might become bottlenecks in the network, causing delays and affecting the overall user experience. Identifying and optimizing these bottlenecks is crucial.
- Inadequate Application Performance: Performance issues with specific applications, such as slow loading times or crashes, can hinder productivity and user satisfaction. These issues often result from application-specific problems or network constraints.
- Network Congestion: When traffic exceeds network capacity, network congestion occurs, leading to slowdowns, increased latency, and potential packet loss.
- Connectivity Challenges: Network connectivity issues when connecting to remote offices, branches, or remote users to the SASE network can disrupt communication and access to resources.
- Hardware Failures: Hardware failures in routers, switches, or other network equipment can lead to network outages and performance issues.
- Network Misconfigurations: Incorrect network configurations can cause routing problems, security vulnerabilities, or misdirected traffic.
- Security Gaps: Incomplete or inadequate security policies can lead to unauthorized access and potential breaches. Identifying and rectifying security gaps is essential for SASE.
- Application Compatibility: Certain applications may not be fully compatible with the SASE environment, causing functionality issues or performance bottlenecks.
- Application Security Flaws: Vulnerabilities in applications can be exploited by malicious actors, leading to breaches and data compromises. Monitoring helps in detecting and addressing security flaws.
- Cloud Service Outages: When relying on cloud-based applications or services, outages or disruptions on the service provider's end can affect application accessibility and performance.
- User Experience Problems: Poorly designed or slow-loading applications can lead to a subpar user experience, reducing productivity and user satisfaction.
- Patch Management: Neglecting to update and patch applications can result in security vulnerabilities, performance issues, or application crashes.
In a SASE environment, monitoring is your first line of defence against a range of performance, network, and application issues. By offering real-time visibility, historical data analysis, alerts, correlation analysis, and robust security incident detection, SASE monitoring empowers organizations to swiftly uncover and troubleshoot problems.
It ensures that your SASE architecture remains resilient, high-performing, and secure, contributing to a seamless user experience and the integrity of your network.
Real-Time Visibility: SASE monitoring provides continuous real-time visibility into your network, applications, and security events. This immediate awareness is invaluable for identifying performance anomalies, security breaches, and other issues as they occur.
Historical Data Analysis: Monitoring solutions capture historical data, allowing you to compare current metrics with past performance. This historical context helps in identifying trends and patterns that could lead to potential issues.
Threshold Alerts: SASE monitoring tools can be configured to generate alerts when specific thresholds are breached. For instance, if latency exceeds a predefined limit or packet loss rates spike, you'll receive notifications, allowing for swift action.
Correlation Analysis: SASE monitoring platforms can perform correlation analysis, helping you connect the dots between different metrics. This aids in pinpointing root causes and understanding how multiple metrics interact to create issues.
Security Incident Detection: Monitoring also acts as a vigilant security guard, continuously scanning for unauthorized access attempts or unusual behavior. It can flag security incidents and provide the data needed to respond effectively.
Comprehensive Reporting: Many SASE monitoring solutions offer detailed reports, making it easier to analyze long-term trends and performance patterns. These reports are valuable for identifying persistent issues and planning for improvements.
Learn about some of the most common network problems that businesses face every day, like high CPU, bandwidth, equipment issues, Internet failures, and more.
Learn more

Your journey through the world of SASE wouldn't be complete without understanding the intricate relationship between monitoring and optimization. Before we leave you to monitor your SASE architecture, let’s look into the symbiotic connection between these two elements and lay out the steps you can take to enhance and fine-tune your SASE architecture for peak performance.
Monitoring and optimization are intrinsically linked within the context of your SASE architecture. Think of monitoring as the watchful eyes that provide real-time data and insights into how your SASE network and security are performing. It's akin to having a dashboard that keeps you informed about the vital signs of your digital infrastructure.
This monitoring data is not just raw information; it's the foundation upon which optimization stands. It is a repository of knowledge that allows you to grasp the current state of your SASE environment.
Optimization is the proactive response to the insights gained through monitoring. Armed with this data, you can take strategic steps to fine-tune and elevate your SASE architecture. Whether it's addressing performance bottlenecks, fortifying security measures, or ensuring efficient resource allocation, optimization is your path to enhancing the overall effectiveness of your SASE setup.
What's more, the relationship between monitoring and optimization doesn't end with a one-time adjustment. It's an ongoing cycle of data-driven improvements. As monitoring continues to provide updated information on the evolving dynamics of your network and applications, you're empowered to make continuous refinements to your SASE architecture, ensuring that it operates at peak performance and security.
Step 1. Identify Performance Bottlenecks: Review the monitoring data to pinpoint performance bottlenecks, such as high latency, bandwidth congestion, or packet loss. Once identified, prioritize resolving these issues to improve the user experience.
Step 2. Review Security Incidents: Examine the security data gathered through monitoring to detect and investigate any security incidents, breaches, or vulnerabilities. Take necessary actions to enhance security and patch any vulnerabilities.
Step 3. Optimize Resource Allocation: Use monitoring insights to allocate network resources effectively. Ensure that business-critical applications receive the necessary bandwidth and prioritize traffic accordingly.
Step 4. Continuous Policy Adjustments: Based on monitoring insights, review and adjust security and access policies. Implement changes to enhance the Zero Trust approach, and ensure that the policies align with the evolving needs of your organization.
Step 5. Capacity Planning: Use historical performance data to plan for future capacity requirements. If you notice trends of increasing resource demand, anticipate these needs and scale your SASE architecture accordingly.
Step 6. Regular Updates and Patches: Monitoring helps identify outdated software, hardware, or security vulnerabilities. Regularly update and patch these components to maintain a secure and optimized SASE environment.
The synergy between monitoring and optimization is the engine that drives a high-performing and secure SASE architecture. It's a continuous cycle of data-driven insights leading to proactive enhancements.

In the journey through the world of Secure Access Service Edge (SASE) monitoring and optimization, we've uncovered crucial insights and explored the intricacies of managing a high-performing, secure digital environment. Here are the key takeaways to keep in mind:
- SASE is the Future: SASE is more than just an acronym; it's a transformative architectural framework that combines network and security services in the cloud, aligning with the evolving digital landscape.
- Monitoring is the Sentry: Effective SASE monitoring is your vigilant sentry, providing real-time data on network performance, security, and user behavior. It's the foundation upon which optimization is built.
- Optimization is the Strategy: Optimization is your proactive response to monitoring insights. It's the continuous process of fine-tuning your SASE architecture to ensure peak performance, security, and efficiency.
- User Experience Matters: Prioritize user experience by monitoring and optimizing performance, ensuring applications run smoothly and securely for remote and mobile users.
- Security is Paramount: SASE is synonymous with security. Monitoring and optimization must align with the Zero Trust model, emphasizing stringent access controls and constant threat detection.
- Data-Driven Decision-Making: Monitoring data is your compass, guiding you toward informed decisions. Optimization is the action that results from that data, ensuring that your SASE environment aligns with your organization's goals.
Now, we encourage you to implement effective SASE monitoring in your IT infrastructure. By doing so, you'll gain real-time insights into your network and security, enabling proactive issue resolution and fine-tuned optimization. Your organization can operate at peak efficiency while maintaining a robust security posture.
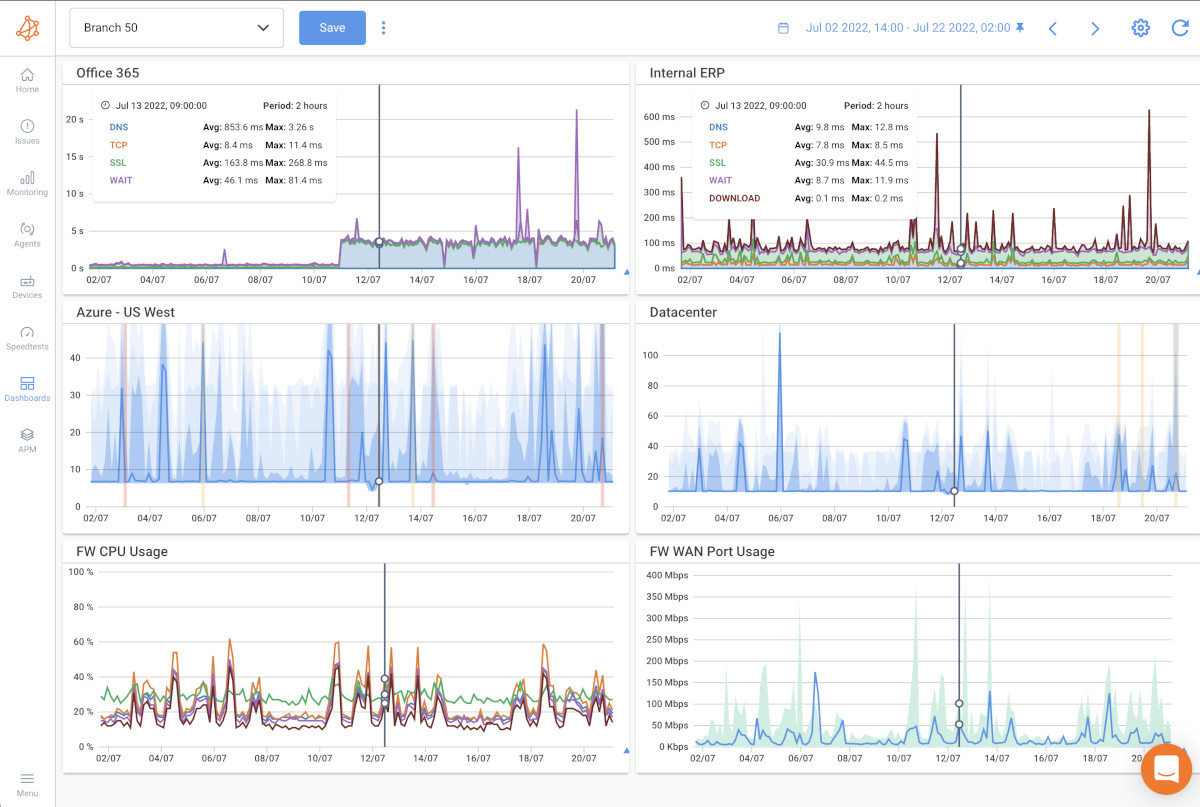
To embark on this journey with confidence and efficiency, we present Obkio's Network Performance Monitoring tool. Obkio offers a comprehensive solution that not only includes Network Performance Monitoring but also Application Performance Monitoring (APM), network device monitoring, and more.
With Obkio, you gain a holistic view of your network, ensuring that your SASE architecture operates at its best. It also provides synthetic monitoring, which allows proactive monitoring without capturing user data, and a distributed monitoring architecture that ensures complete coverage.
Make the commitment to empower your organization with effective SASE monitoring and optimization. Start your journey with Obkio, assemble your monitoring Avengers, and keep your SASE realm secure and efficient. Your digital future awaits—seize it with confidence and Obkio's Network Performance Monitoring tool by your side.





























 Obkio Blog
Obkio Blog